
The Lamp That Did Not Know It Was Burning
There was once a monastery that sat at the crossroads of three great roads. Merchants came from the north. Pilgrims came from the east. And from the west, sometimes, came those whose intentions could not be easily read from their faces.
The monastery kept a lamp at its gate. Not a large lamp. Just enough light to guide the weary traveler through the darkness. The monks tended it faithfully, trimming the wick each morning, refilling the oil each evening. They were proud of their lamp. They spoke of it often.
They told travelers, "This light has burned for three hundred years without interruption."
One winter, a group of travelers arrived from the west. They were well-dressed. They spoke politely. They praised the monastery, admired its gardens, and asked if they might rest within its walls for a few days while the mountain passes cleared of snow.
The abbot welcomed them. Hospitality was the monastery's oldest practice.
The travelers stayed. They were helpful. They carried water. They repaired a section of the outer wall that had crumbled. They laughed with the younger monks and listened respectfully to the elder ones. Some of the novices began spending their evenings in conversation with the travelers rather than in study.
One of the novices, a young monk named Arjun, noticed something in the third week. Each night, one of the travelers would walk to the gate and stand near the lamp for a long time. Not looking at the road. Looking at the lamp itself. Studying how it was constructed. Where the oil was stored. How the wick was trimmed.
Which monk tended it and at what hour?
Arjun brought this to the abbot.
The abbot was quiet for a long time. Then he said, "What do you think the traveler is doing?"
Arjun said, "I think he is learning how to put it out."
The abbot was quiet again. Then he said, "And what did you do when you saw this?"
Arjun said, "I came to you."
The abbot shook his head slowly. He said, " You came to me. But the lamp is still at the gate. And the traveler is still at the lamp."
Arjun understood. He rose and went to the gate. He stood beside the lamp himself. He said nothing to the traveler. He simply stood there through the night, tending the flame, present and awake.
In the morning, the travelers left. They thanked the monks for their hospitality. They praised the monastery again. They said they would tell others of its generosity.
When they had gone, the abbot called all the monks together. He said, "What did we learn?"
One monk said, "We should not trust strangers."
The abbot shook his head.
Another monk said, " We should build a wall around the lamp."
The abbot shook his head again.
A third monk said, "We should have sent them away when they first arrived."
The abbot looked at each of them in turn.
Then he said, "None of you have understood."
The lamp was in danger from us.
From our pride in tending it without watching it. From our belief that three hundred years of burning was proof that it could never be extinguished.
From our hospitality that became blindness. From our welcome that asked no questions. From our comfort that mistook stillness for safety.
He said, "A flame does not know it is burning. That is why it needs a keeper who is awake."
He said, the travelers studied our lamp because we had stopped studying it ourselves. They knew its vulnerabilities before we did because we had decided it had none.
He paused. Then he said, Arjun watched. Arjun stood. Arjun did not come to me first to ask permission to protect what was already his to protect. He acted. This is what it means to be a keeper.
He looked at the lamp burning at the gate in the morning light.
He said, "The question is not whether those who wish to extinguish your flame will come. They will always come. They have always come. The question is only whether you are awake enough to stand beside what you love when they arrive. And whether you have made peace with the fact that standing there will cost you a night of sleep, and perhaps many nights, and perhaps more than sleep."
A young novice at the back of the assembly raised his hand. He asked, but Abbot, how do we know when a traveler is a traveler and when a traveler is something else?
The abbot smiled for the first time that morning. He said that was the right question. That is the only question. And the answer is this: you know when you are watching. You do not know when you have decided that watching is unnecessary.
He dismissed the assembly. He walked to the gate himself. He trimmed the wick. He checked the oil. He stood for a moment with his hand near the flame, close enough to feel its warmth, and looked out at the three roads stretching away into the distance.
Then he went inside for his morning prayers, leaving Arjun awake at the gate.
The Operation
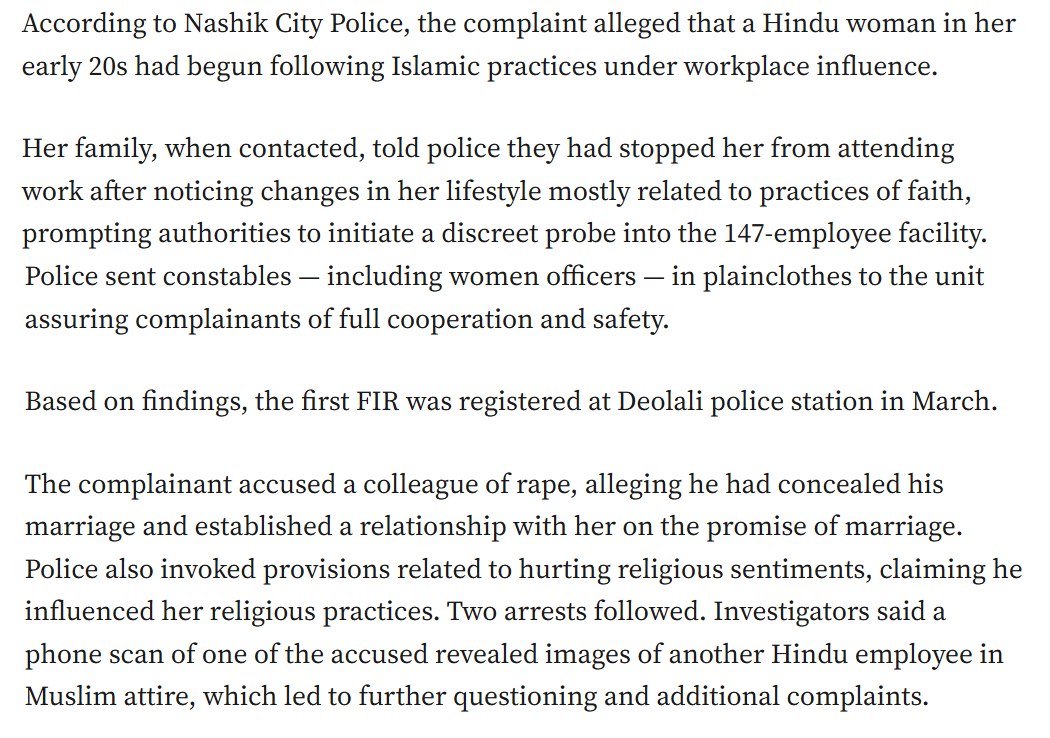
The first complaint was filed on March 26, 2026. By mid-April, the scale of what had been operating inside one of India's most prestigious IT companies for four uninterrupted years had become visible enough that even India's Supreme Court took note.
Something happened in a Tata Consultancy Services BPO office in Nashik, Maharashtra, that India's political and media establishment has struggled to name correctly. Nine First Information Reports. Seven arrests. A Special Investigation Team. Parallel investigations by the Anti-Terrorism Squad, the National Investigation Agency, and the Intelligence Bureau. Six women police officers deployed undercover for 40 days, posing as employees inside the facility to corroborate what no internal mechanism had been willing to document.
The accused are eight individuals, six male team leaders and two women, one of whom, HR functionary Nida Khan, remains the subject of an active search while her lawyers seek anticipatory bail on grounds of pregnancy. The named accused are Danish Sheikh, Tausif Attar, Raza Memon, Shahrukh Qureshi, Asif Ansari, Shafi Sheikh, Nida Khan, and Ashwini Chainani. They occupied positions of institutional authority over young Hindu women, primarily in their early to mid-twenties, many from financially vulnerable families, many newly relocated from their home districts, many at the start of careers that represented the first real economic foothold their families had secured.
What those accused are alleged to have done, across four years inside a corporate facility of a company trusted with India's most sensitive national examination infrastructure, is the subject of this analysis. What it means for India's national security, its economic credibility, its civilizational integrity, and its political future is the question this analysis attempts to answer with the rigor the facts demand and the seriousness the victims deserve.
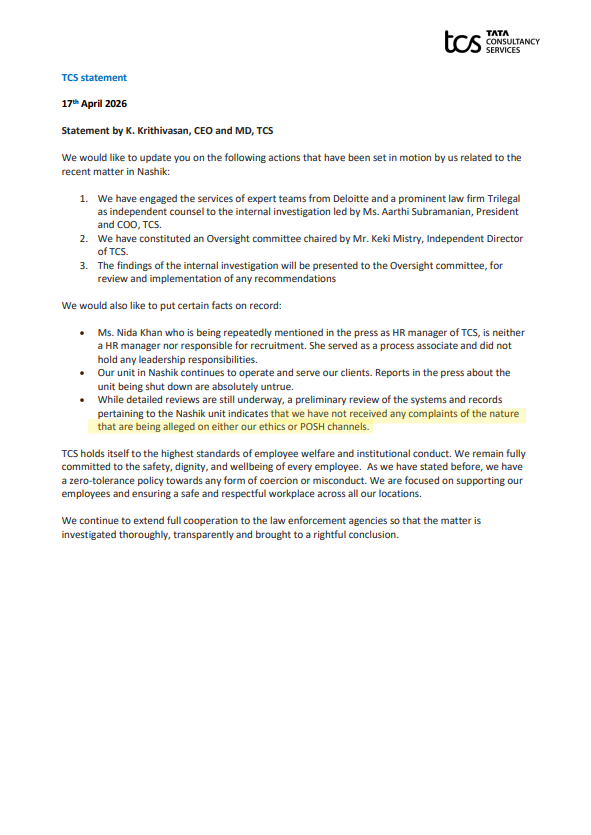
TCS issued a perfunctory statement that is remarkable for its lack of seriousness. Worse, it shows an ugly attempt at denying what happened.
To say that "we have not received any complaints of the nature that are being alleged on either our ethics or POSH channels," is spectacularly suicidal and facetious at the same time. Most importantly, because the police had done an extensive sting undercover operation, where they had collected a large amount of information and forensic data.
Source: X Post from TCS
Police registered nine FIRs between March 26 and April 3, 2026. Key allegations include:
- Sexual harassment, molestation, stalking, coercion into sexual relationships, and at least one case of rape under the promise of marriage.
- Mental exploitation and pressure on female employees (primarily Hindu, per some reports) by a group of male colleagues and at least one woman.
- Attempts at forcible religious conversions or influence, such as pressuring women to adopt Islamic practices, with claims of concessions for prayers to one community and extra work for others.
- Some victims alleged that complaints to HR were ignored, blocked, or discouraged for years, pointing to possible HR complicity or failure under the POSH (Prevention of Sexual Harassment) Act.
Police described the male accused as operating like an "organized gang" or "syndicate" targeting female colleagues. Two suspended TCS employees, Tausif Attar and Nida Khan, were identified by some investigators as potential masterminds.
Additional claims from media interviews and employee accounts (e.g., on Republic TV) included grooming, extra-workload discrimination, and links to external influencers. This Malaysia-linked preacher is under the scanner now.
The police involvement started when the family of one of the victims shared their concerns with the police administration within Nashik.
Police work is ongoing, so information is trickling out in dribs and drabs.
The Public Sharing by the Nashik police is limited to summaries. Nashik police published an official notice (in Marathi) detailing the investigation's scope, the undercover operation, and observations of harassment and religious pressure. It is available via police channels (e.g., a PDF hosted on their site).
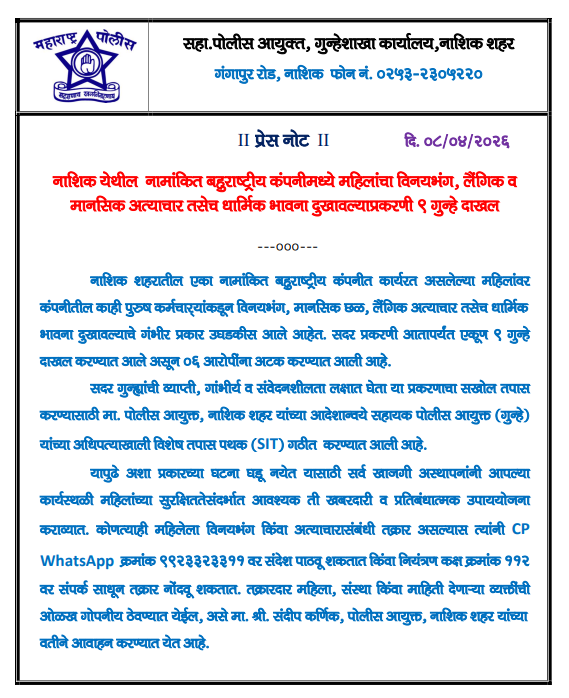
Details have been shared in court hearings (e.g., the prosecutor mentioning emails, call records, and the need for analysis). Police commissioner Sandeep Karnik and SIT officers have briefed the media on high-level findings (e.g., "40 CCTV clips," "78 emails," WhatsApp patterns) without, however, releasing raw files
Case details have been shared by Nashik Police with NIA, ATS, and intelligence agencies for possible foreign/extremist links or funding.
So, the probe into the 9 FIRs remains with the Nashik SIT, while the broader angles have been referred to other agencies.
Raw chats, full CCTV footage, or complete forensic reports have not been publicly released, which is a standard practice in such ongoing cases to avoid tampering or victim identification issues. Police have also warned against media/social media revealing victim identities.
So what information is publicly available?
Full FIR copies have not been officially shared publicly by police in a downloadable or widespread manner (again, to safeguard privacy and the investigation).
However:
- Details from FIRs have been widely reported based on access by media outlets and court proceedings.
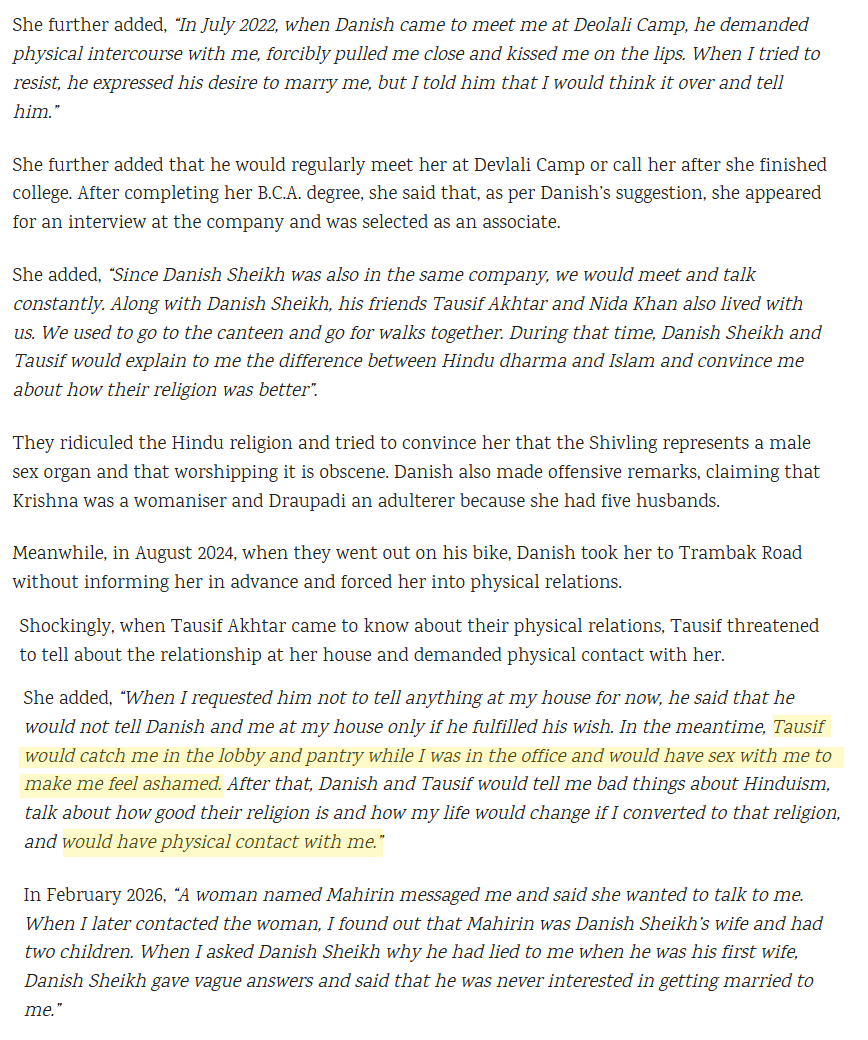
- The first FIR (No. 156/2026 at Devlali Police Station, filed March 26, 2026): A detailed rape complaint against Danish Sheik (or similar spelling), alleging a relationship from 2022, false promise of marriage, repeated sexual acts (including inside the office), and religious influence. It was later expanded to include SC/ST Act sections.
The Organiser magazine has shared that they have been able to access and summarize its contents.
- Overall: Nine FIRs registered (March 26–April 3, 2026) across Devlali and Mumbai Naka stations. Eight by women (sexual offenses + religious harassment); one by a male employee. Charges include rape, sexual harassment, stalking, outraging modesty, and hurting religious sentiments. Accused named across FIRs include Danish Sheikh, Tausif Attar, Raza Memon, Shafi Sheikh, etc., plus HR figures.
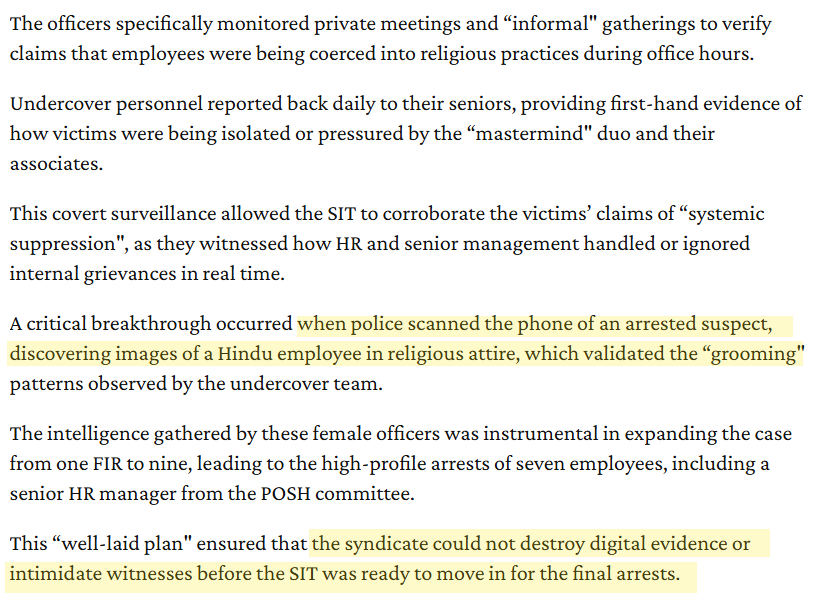
Police gathered direct, circumstantial, and digital evidence through a ~40-day undercover operation (involving 6–7 women officers posing as employees or housekeeping staff), victim statements, device seizures, and internal records.
Digital Communications:
- WhatsApp chats and groups: Multiple groups allegedly used for grooming, building trust, isolating victims, and pressuring them (including religious influence and sexual coercion). Chats recovered from the arrested suspects' phones. One breakthrough: images of a Hindu employee in religious (Islamic) attire found on a suspect's phone, validating grooming claims.
- Call detail records (CDR): Analysis of calls, including 38 conversations between a senior HR/AGM figure and one accused, plus another call with a second accused.
- Emails: Over 78 emails seized, plus additional internal emails and a specific chat from an Assistant General Manager's (AGM) devices. These reportedly show complaints being forwarded to seniors but allegedly ignored or suppressed by HR/POSH committee members. Emails are being examined in the presence of the accused.timesofindia.indiatimes.com
CCTV Footage: Over 40 CCTV clips examined by the SIT. Footage is being scrutinized for instances of harassment, meetings, isolation of victims, and workplace interactions. Some reports mention monitoring via company CCTV during the undercover phase.
Victim and Witness Statements: Beyond all this, the police undercover operatives also gathered direct information.
- Direct accounts from more than 8 women (and 1 man) detailing rape (under false promise of marriage), repeated molestation, stalking, lewd comments, mental exploitation, and religious pressure (e.g., observing Ramzan fasts, head covering, or other practices).
- Undercover officers provided firsthand observations of patterns: the isolation of victims, pressure tactics, and HR allegedly discouraging complaints ("These things happen"). They reported daily to seniors.
Other Forensics and Physical/Digital Seizures: They are also checking on the phones and the bank accounts.
- Mobile phones and devices of the accused: Forensically scanned for chats, images, call logs, and deleted data.
- Potential bank statements of key figures (e.g., the AGM) to check for financial links or transactions.
- Broader probe into possible external links (e.g., a Malaysia-linked preacher or individual named Imran in WhatsApp chats discussing jobs abroad).
The Hindu, a rabid anti-Hindu newspaper, also shared the nefarious activities.
“Both Mr. Tausif and Ms. Nida would try to brainwash other employees. After Mr. Tausif returned from Mecca three years ago, his views became extremely radical. He used to say Islam is the only religion and speak ill of Hinduism. He would brainwash others to accept Islam and tried to convince an employee that his father would be cured of paralysis if he accepted Islam. He also raped a victim on the false promises of marriage while concealing facts that he was already married and had two children. The accused duo managed to completely change the victim’s belief. She had started reciting Kalma, wearing burqa and offering namaz,” according to police. “Ms. Nida used to introduce young women to the accused and constantly talk ill about Hinduism. She was the one who taught the victims how to offer namaz and recite Kalmas,” the police added. (Source: "TCS Nashik case: two suspended employees masterminds, say police" / The Hindu)
The rot may not be limited to just Nashik. Many employees in other cities are also coming out.
Now news from TCS Kolkata.
— Monidipa Bose - Dey (মণিদীপা) (@monidipadey) April 17, 2026
Same conversion gang operating there!
Hello @TCS what exactly is your business model? Conversions ? @NIA_India @HMOIndia please note.
Image was Shared with me by @MeriJaanBharat pic.twitter.com/ymd10Gm7wS
The bug of one-sided and bigoted idea of Secularism is proliferating across India's corporates and media companies. That, as we will discuss later in more detail, is the basis for creating a happy hunting ground for molesters and rapists using Islam as the tool to probably do something more dangerous.
The latest case of Lenskart is quite instructive. While restrictions were excessively imposed on Hindus, no such restrictions were imposed on Muslims.
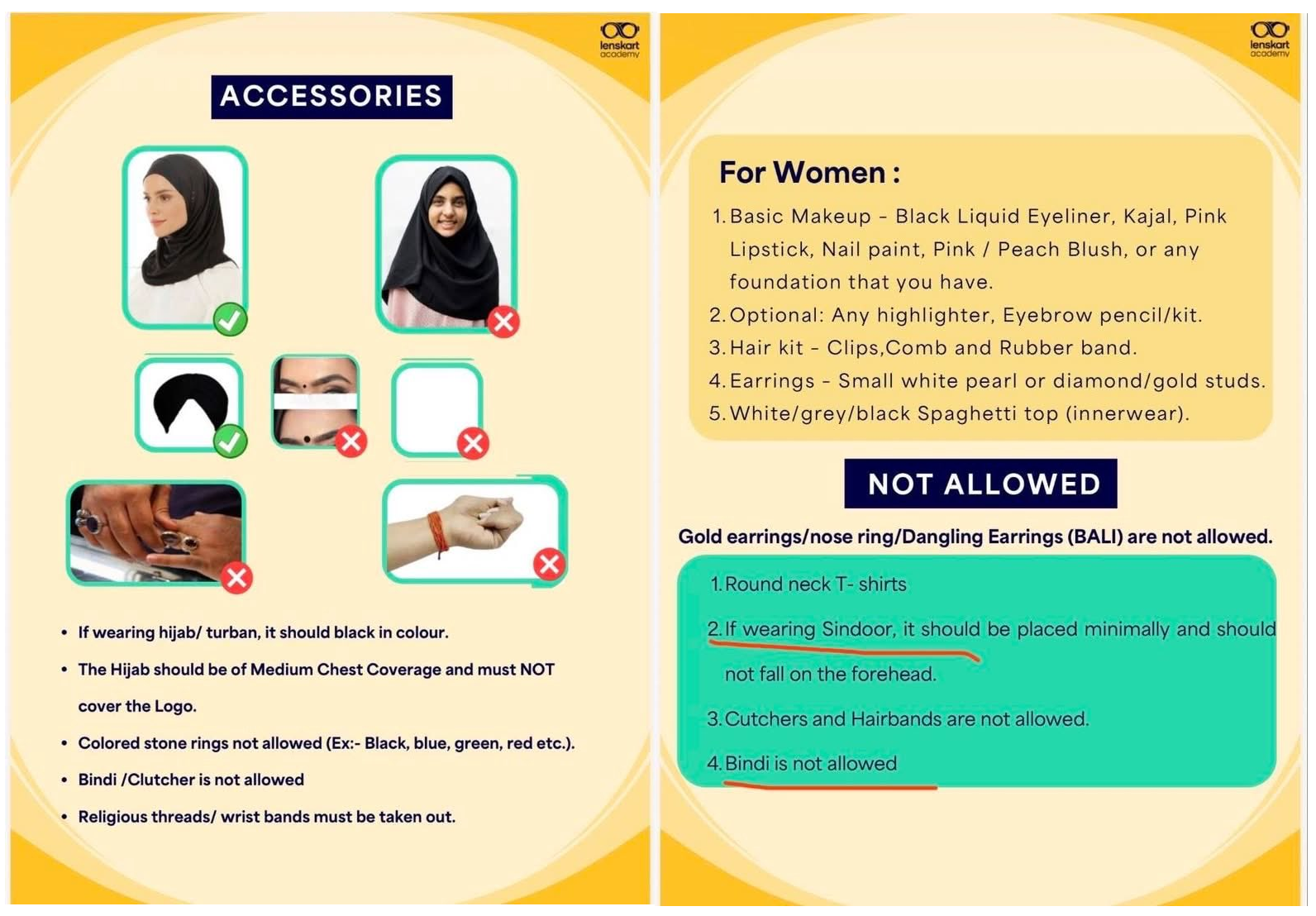
Despite the denials from the company's administration, the evidence and testimonials from the public are quite overwhelming.
Let us look at one.
Take a listen.
It is in this atmosphere of perfect situation for abusive and persecutory existence of Hindu employees that the TCS Nashik case occured.
That is why this analysis treats the TCS Nashik case as what the evidence compels us to treat it as: a structured, organized, multi-year, religiously motivated operation targeting Hindu employees in a corporate setting.
Secular Denialism
The reactions from the so-called "Secular Operatives" in India have been along expected lines.
The standard frames being applied to this case by those who wish to minimize it are three.
- The first is the workplace misconduct frame, which treats what happened as a failure of HR governance and POSH compliance.
- The second is the communal relations frame, which processes it as another episode in Hindu-Muslim tension requiring measured response and appeal to brotherhood.
- The third is the political convenience frame, which reads the entire episode as BJP mobilization using victim suffering as electoral fuel.
All three frames are wrong.
They are wrong because the evidence does not fit them.
It is, plain and simple, organized predation with foreign coordination.
Calling it a communal relations problem is the equivalent of calling Operation Searchlight a border dispute.
This analysis calls it what the evidence compels it to be called.
It connects to a documented global infrastructure of ideological production, financial transit, and operational coordination that has been targeting Hindus as a specific group across the Indian subcontinent for over 75 years
With that, let us fully grasp the gravity of the case.
What Four Years Without Leaks REALLY Means
This is the most important question for any analysis in this matter.
We are looking at at least 4 phases of this operation.
Phase 1: Pre-Insertion — Recruiting Into the Network
An operation of this nature does not begin on Day 1 at TCS Nashik. It requires a pre-existing network that identifies the target environment and decides to deploy into it.
Several elements would have been required before a single operative walked through TCS's doors.
- The BPO/IT sector was specifically chosen as the target environment. This reflects deliberate selection logic. BPO environments carry specific vulnerabilities:
- high female employment,
- a young workforce,
- geographic relocation from families,
- hierarchical power structures,
- team-leader authority over career advancement, and
- relatively low social capital among new employees who are far from support networks.
An operation designed to exploit exactly these vulnerabilities did not stumble into this sector by accident.
A full-fledged network was active, including individuals in higher positions, such as team leaders. These individuals systematically targeted Hindu women. So the contours and details of this entire operation (and wider cohorts) would have been painstakingly planned.
- Team leader positions are not entry-level. They require time, performance history, and internal recommendations. More importantly, a resume with a work history!
- Either the accused were placed strategically, meaning someone coordinated their placements, or they ascended to these positions over time while the broader operation waited for them to gain sufficient authority.
- Both scenarios require multi-year planning.
The HR penetration is the most operationally significant element of Phase 1.
The fact that HR head Nida Khan is now the primary absconding accused, and that HR consistently dismissed complaints, is a structural feature of the operation rather than a coincidence.
Phase 2: Operational Security — Four Years Without Leaks
This is the most significant analytical datapoint in the entire case.
For a network of at least eight identified accused to operate continuously for four years without a single complaint triggering action requires multiple simultaneous systems working in coordination.
- Victim isolation was the first system. Danish would emotionally influence the women by telling them, "Your family members do not love you, don't ruin your lives for them." Separation from family support networks is standard cult and grooming methodology. It ensures that even when victims feel distress, they have no trusted external person to report to. An isolated victim is a contained risk.
- Complaint suppression architecture was the second system. Victims had allegedly complained to her earlier, but no action was reportedly taken at the time. With HR captured, every complaint went into a black hole. Victims who complained and saw no action learned that the institution would not protect them. This produced the sustained silence the operation required.
- Blackmail insurance was the third system. Police sources confirm the SIT is examining digital evidence, including alleged WhatsApp coordination groups and blackmail material. Sexual blackmail material, once obtained, ensures that victims who might otherwise report have something to lose by doing so. The overlap between sexual exploitation and blackmail production is a deliberate operational feature.
- Financial control was the fourth system. The bank account manipulation described above means victims developed financial dependency on or vulnerability to the accused, creating an additional deterrent to reporting that operated independently of shame or fear.
- Collective silence among perpetrators was the fifth and most telling system. Operating for four years while maintaining operational security is not achievable among random individuals who happen to share an ideology. It requires prior network formation, established trust, shared incentive structures, and possibly external oversight that none of the floor-level accused would have been in a position to provide themselves.
That raises questions about how deep and how far-reaching this operation was.
Phase 3: The Handler Model
If the handler model holds, then the HR head who is now absconding is not the originator of the operation.
She is the local executor of a methodology that someone above her designed, and that is almost certainly running, in some form, in other offices in other cities right now.
The handler model, in which local operatives execute a doctrine designed and monitored externally, is consistent with all the evidence in this case.
The Malaysia preacher connection is the most important operational detail because it provides the external coordination node.
According to investigators, the WhatsApp chats further disclosed that a Malaysia-linked preacher, Imran, was introduced to the victims via video calls.
A preacher being introduced to victims via video call during the grooming process is a structured introduction at a specific stage of the conversion process.
Phase 4: Could This Have Operated Without Cover Elsewhere in TCS?
This is the question the SIT and central agency investigation must answer rigorously.
Consider what would have been organizationally necessary for this to continue undetected for four years.
Either screening was deliberately weakened, or the placements were assisted internally by someone with hiring authority above the team leader level.
Manager-level passivity above the team leaders was equally necessary. Above the team leaders, there are managers and senior managers.
The operation required that this level remain either unaware or non-interventionist for four years across multiple complaints from multiple victims.
IT and digital monitoring would also need to have had consistent gaps.
Large IT companies have digital monitoring capabilities.
The geographic replication pattern makes the single-office explanation even less plausible.
Anonymous testimonies, early media reports, and FIR filings point to similar operational signatures in IT and BPO environments across Hyderabad, Pune, Kolkata, and Mumbai: clusters of managers and HR personnel from one community; differential leave and shift policies informally tied to religious observance; organized social events used as grooming vectors; and, most significantly, the consistent mocking of Hindu belief as a tool of psychological degradation.
And that is why we come to the next obvious question:
Why Grooming Jihad Should Be Considered Hindu Genocide
For this exercise, we first need to understand the history of the concept of Genocide.
Raphaël Lemkin (1900–1959), a Polish-Jewish jurist, coined the term “genocide” in 1942 and spent the rest of his life ensuring it became a crime under international law. Deeply affected by the atrocities of World War II and having lost 49 members of his own family in the Holocaust, Lemkin sought a word that captured not just mass killing but the systematic destruction of entire human groups.
This included a wide range of actions: killing members of the group, causing serious bodily or mental harm, deliberately inflicting conditions of life calculated to bring about physical destruction, preventing births, and forcibly transferring children.
After the war, Lemkin worked with Robert H. Jackson, the chief U.S. prosecutor at the Nuremberg Trials. However, he was dissatisfied that “genocide” was not yet formally recognized in international law, which limited the scope of justice against Nazi crimes. This gap drove his relentless advocacy at the United Nations.
His efforts culminated in the adoption of the Convention on the Prevention and Punishment of the Crime of Genocide on December 9, 1948. The convention codified Lemkin’s vision, defining genocide as acts committed with the intent to destroy, in whole or in part, a national, ethnic, racial, or religious group—embedding his expansive and preventative understanding of the crime into international law.
Now, let us dive deeper.
The Mechanism of Harm is Identical
Some scholars have argued that the Convention on the Prevention and Punishment of the Crime of Genocide should more explicitly recognize mass rape—particularly when carried out with the intent to forcibly impregnate women of a targeted group—as an act of genocide. Others contend that such acts are already encompassed within Article II of the Convention, which defines genocide to include measures intended to prevent births within a group or to destroy it in whole or in part.
Legal theorist Catharine MacKinnon argues that genocidal rape operates as a deliberate strategy aimed not merely at individual victims, but at the destruction of the targeted ethnic or religious community itself.
In her seminal essay on this topic, McKinnon shared her idea, which laid out the contours of the new and very obvious dimension of genocidal operations.
Atrocities committed against women are either too human to fit the notion of female or too female to fit the notion of human. In an international world order in which only states can violate human rights, most rape is left out. Women are violated sexually and reproductively every day in every country in the world. The notion that these acts violate women's human rights has been created by women, not by states or governments. In the genocide through war, mass rape is a tool, a tactic, a policy, a plan, a strategy, as well as a practice. The camps can be outdoor enclosures of barbed wire or buildings where people are held, beaten, and killed and where women, and sometimes men, are raped. Sometimes the women are also raped after they are killed. A war crimes tribunal to enforce accountability for mass genocidal rape is being prepared by the United Nations. (Source: Rape, Genocide, and Women’s Human Rights by Catharine A. MacKinnon)
Building on this reasoning, Siobhan Fisher emphasizes that the critical threshold is crossed when rape is carried out with the intent to impregnate. According to this perspective, forced impregnation transforms sexual violence into a genocidal act by seeking to alter the demographic and biological continuity of the targeted group—either by imposing the perpetrator’s lineage or by undermining the group’s ability to reproduce itself on its own terms.
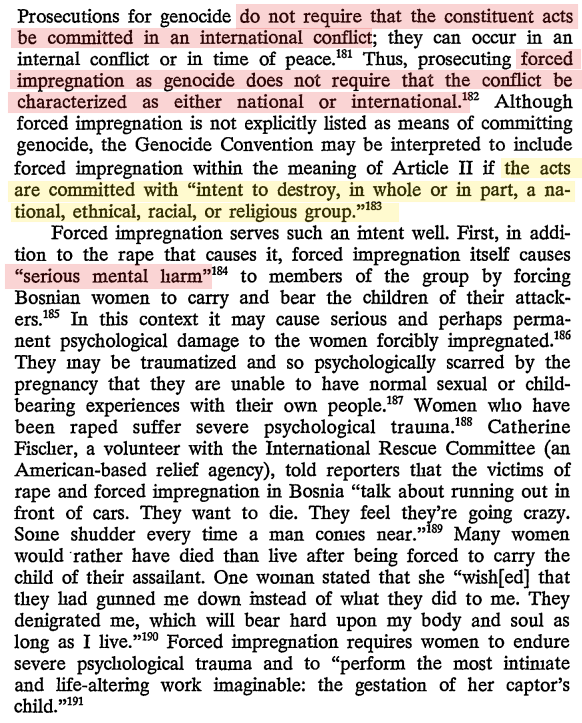
Fisher's Duke Law Journal piece identifies three specific mechanisms by which forced impregnation constitutes genocide under the 1948 Convention:
- It causes serious mental harm to members of the group (Article II(b))
- It deliberately inflicts conditions of life calculated to bring about physical destruction of the group (Article II(c))
- It imposes measures intended to prevent births within the group (Article II(d)) — because a woman occupied with bearing a perpetrator's child cannot simultaneously bear a child of her own community
However, Lisa Sharlach cautions against narrowing the definition of genocide too strictly to cases of forced impregnation alone. She argues that mass rape, even without resulting pregnancy, can function as a tool of group destruction through terror, displacement, social fragmentation, and long-term psychological and cultural damage. Limiting the definition solely to impregnation risks overlooks the broader genocidal intent embedded in systematic sexual violence.
Her 2000 article in New Political Science, "Rape as Genocide: Bangladesh, the Former Yugoslavia, and Rwanda," established that mass rape without resulting pregnancy still qualifies as a genocidal instrument under Articles II(b) and II(c) of the 1948 Genocide Convention, because it causes serious mental harm to members of the group and deliberately inflicts conditions of life calculated to bring about the group's physical destruction.
According to the 1948 Convention on the Prevention and Punishment of the Crime of Genocide, causing serious bodily or mental harm to members of an ethnic, national, or religious group and/or ''deliberately inflicting on the group conditions of life calculated to bring about its physical destruction in whole or in part'' constitute genocide. Rape certainly may cause serious physical and/or mental injury to the survivor, and also may destroy the morale of her family and ethnic community. However, this Convention does not explicitly state that sexual violence is a crime of genocide. The Convention should be expanded to include mass rape, regardless of whether the victims are raped on the basis of racial/ethnic, national, or religious identity. (Source: "Rape as Genocide: Bangladesh, the Former Yugoslavia, and Rwanda" by Lisa Sharlack / Pages 89-102 | Published online: 18 Aug 2010)
Sharlach's framework, when combined with the Lemkin-based social death analysis from the uploaded scholarship, produces the following argument: systematic sexual violence targeting women on the basis of their group identity, whether in a rape camp in Dhaka in 1971, a detention facility in Foča in 1992, or a BPO office in Nashik in 2022, constitutes a genocidal instrument when it is organized, group-targeted, and produces foreseeable social destruction of the victim community.
The mechanism of delivery changes. The ideology animating it, the targeting logic, and the civilizational objective do not.
Bangladesh 1971: The Foundational Case
To understand what is happening in Nashik, you must first understand what happened in Dhaka in 1971, because the two events share the same ideological DNA. Operation Searchlight was not a military excess. It was a planned, command-authorized genocide with a specific Hindu targeting logic embedded at the highest levels of the Pakistani military establishment.
In 1971, the self-appointed president of Pakistan and commander-in-chief of the army, General Agha Mohammed Yahya Khan, and his top generals prepared a careful and systematic military, economic, and political operation against East Pakistan.
They planned to murder that country's Bengali intellectual, cultural, and political elite. They planned to indiscriminately murder hundreds of thousands of its Hindus and drive the rest into India. And they planned to destroy its economic base to ensure that it would be subordinate to West Pakistan for at least a generation to come.
The Hindu targeting within this plan was explicit, deliberate, and theologically framed.
A disproportionate number of Hindus were killed in 1971. In that year, Hindus were some 20% of East Pakistan's population, yet it was estimated that they might have been 50% of those killed. According to Rudolph Joseph Rummel, in the eyes of Western Pakistanis and their fundamentalist Muslim collaborators, the Hindus among the Bengalis were as Jews to the Nazis, scum and vermin that should best be exterminated. The parallel with the Nazi persecution of Jews is made even more appropriate by the fact that the Western Pakistani army compelled Hindus to have a yellow "H" painted on their homes, thus designating those who lived there as targets for extermination.
Lt. Colonel Aziz Ahmed Khan reported that in May 1971, there was a written order to kill Hindus, and that General Niazi would ask troops how many Hindus they had killed.
In what became province-wide acts of genocide, Hindus were sought out and killed on the spot. As a matter of course, soldiers would check males for the obligatory circumcision among Muslims. If circumcised, they might live; if not, sure death.
This is religiously predicated genocide and not mere "racial profiling".
The targeting criterion was being Hindu. The instrument for identification was the absence of circumcision, which in the subcontinental context is a religious marker.
The Pakistan Army was literally separating Hindus from Muslims on the basis of their bodies and killing the former on the spot.
Yahya Khan's reported statement, "Kill three million of them, and the rest will eat out of our hands," preceded the operation as a command-level framing document.
The sexual violence within this operation was equally command-sanctioned and equally Hindu-targeting in its primary logic.
During the 1971 Bangladesh war for independence, members of the Pakistani military and supporting Islamist militias raped between two and four hundred thousand Bangladeshi women in a systematic campaign of genocidal rape.
During the war, a fatwa in Pakistan declared that the Bengali freedom fighters were Hindus and that their women could be taken as the booty of war. Imams and Muslim religious leaders publicly declared that the Bengali women were gonimoter maal, meaning war booty, and thus openly supported the rape of Bengali women by the Pakistani Army.
West Pakistani men wanted to cleanse a nation corrupted by the presence of Hindus and believed that the sacrifice of Hindu women was needed; Bengali women were thus viewed as Hindu or Hindu-like. These rapes apparently caused thousands of pregnancies, births of war babies, abortions, infanticide, suicide, and ostracism of the victims.
Many historians believe the violent campaign of mass rape to have been a direct policy under Khan's command to impregnate as many women as possible with blood from West Pakistan. During the conflict, military-style rape camps were set up across the country.
The "blood from the west" framing is the same sperm-as-weapon logic that Beverly Allen documented in the Bosnian case.
The intent was identical:
- use sexual violence and forced impregnation to biologically and culturally contaminate the target group,
- destroy the social vitality of its women,
- prevent reproduction within the group,
- produce children who would be neither fully of the mother's community nor of the perpetrators', and
- ensure that the social fracture this produces would reverberate across generations.
The Archer Blood cable to Washington, which gave Gary Bass's book its name, documented all of this with diplomatic precision in real time.
The fact that Nixon and Kissinger were cognisant of the conditions on the ground in East Pakistan is made clear through the existence of diplomatic cables, sent from the US consulate in Dhaka, describing the brutality unleashed by the Pakistani military in its attempts to quell the Bengali nationalist movement. The Blood Telegram gets its name from Archer Blood, the US consul general in East Pakistan during 1971, and the telegram he sent to the State Department on April 6, 1971. In what is widely believed to be perhaps the most strongly worded note of dissent sounded by an American diplomat against the policies of the US government, Blood accused Nixon and Kissinger of “moral bankruptcy” for their failure to act against a West Pakistani regime that had started a systematic campaign of violence that targeted Dhaka’s Hindu population, as well as Bengali nationalists and their sympathisers. For Archer Blood, the word “genocide” was an apt description for what had been taking place in Dhaka since the initiation of Operation Searchlight by the Pakistani military on March 25. Archer Blood and his staff had been in Dhaka since the start of the operation, in which students and professors at Dhaka University had been massacred by Pakistani troops, and had continued to bear witness to the killing of thousands of mostly Hindu Bengalis over the course of the next two weeks. (Source: COVER STORY: The Blood Telegram by Gary J. Bass by Hassan Javid / The Dawn)
Archer Blood and his cohorts in the American consulate in Dacca reported an accurate description of the mass killings by West Pakistani troops in the east, particularly Hindus, who made up only 16 to 17% of the population, but were 90% of the refugees.
The Ideological Architecture: What Connects 1971 to Nashik 2026
The genocide studies literature is explicit about what distinguishes a series of events from a sequence of unrelated crimes.
Lemkin's framework requires a coordinated plan with genocidal aim, implemented through multiple techniques across political, social, biological, physical, religious, and moral dimensions, with the cumulative and foreseeable consequence of destroying the foundations of a group's life.
The question before us is whether a continuous ideological thread connects Operation Searchlight's Hindu-targeting logic to the grooming operations documented in Nashik and across India's IT sector. The answer requires examining the ideology itself.
The dehumanization of Hindus within certain Pakistani military and Islamist intellectual traditions did not begin in 1971 and did not end in 1971. It is a documented, persistent, and institutionalized frame.
The specific elements of that frame, as documented in 1971, are:
- Hindus are impure contamination in an Islamic space;
- Hindu women are targets for sexual conquest because their bodies represent the honor and continuity of the Hindu community;
- the rape, conversion, and impregnation of Hindu women simultaneously punishes the community, diminishes its future, and asserts Islamic dominance; and
- the children produced by these unions represent not just the perpetrator's lineage but the destruction of the victim community's demographic and cultural continuity.
What makes the mocking of Sanatan Dharma, the insistence on eating beef, and the forcing of namaz on Hindu employees in Nashik not merely cultural insensitivity or aggressive proselytizing is that they are ritual assertions of dominance, the theological vocabulary of occupation.
The ritual vocabulary in Nashik is identical to the ritual vocabulary in Dhaka in 1971.
The Pakistan Army compelled Hindu victims to undergo religious humiliation before execution. The Nashik accused compelled Hindu victims to recite Islamic prayers, eat beef, observe Ramzan fasts, and verbally repudiate their own gods.
It is the assertion of religio-civilizational dominance through the degradation of the victim's religious identity as a precondition for the sexual, economic, and social violation that follows.
The scale is radically different. The mechanism of delivery is radically different. The ideological structure generating both events is not different.
One of the victims stated, I started working in the company in 2022. At that time, Tausif Attar, Danish Sheikh, and others were working in my team. Tausif and Danish would make me do extra work. They made me wear their religious cap and recite namaz while using abusive language against the gods of my religion. They insulted Hindu gods and Hindu dharma and tried to convert me by forcing me to eat non-vegetarian food. When I opposed them, they targeted me at work and abused me. They also made obscene remarks about women in the Hindu dharma. Therefore, I have filed a legal complaint against them. (Source: "Your god doesn’t exist, only Allah does”: TCS Nashik employee details religious coercion & abuse to Hindu gods" / Organiser)
The pattern documented across the nine Nashik FIRs is the pattern documented in every case of organized grooming operation targeting Hindu communities: sexual approach combined with religious derogation, followed by exploitation, followed by conversion pressure, followed by isolation from family and community.
The sequence is not random. It is a methodology. And methodologies do not emerge from individual pathology.
They are taught, shared, refined through networks, and deployed by operatives who have been trained in them.
Sharlach's Framework Applied: Why This Is Genocide Without Requiring Pregnancy
Sharlach's specific contribution to the analytical framework is the argument that even without impregnation, systematic sexual violence targeting a group on the basis of group identity produces genocidal consequences through the mechanisms that the Genocide Convention already recognizes.
Applying her framework directly to the Nashik case and the pattern it represents across India's IT sector produces the following analysis.
Serious mental harm to members of the group is the first mechanism.
The Nashik testimonies document exactly the psychological destruction Sharlach identifies as genocidal. Victims described symptoms consistent with severe PTSD.
One testified that her perpetrator had sex with her in lobbies and pantries to make her "feel ashamed."
Another described being told that her family did not love her and that she should abandon them.
Multiple victims left their employment rather than continue enduring the harassment, which means the workplace, their economic future, and their social status were all destroyed by the operation.
Deliberately inflicting conditions of life calculated to bring about physical destruction of the group is the second mechanism.
Terror, displacement, and community fracture are the third mechanism, drawn directly from Sharlach's expansion of the genocidal framework beyond impregnation.
She documented in the Bangladesh case that mass rape produces community displacement through the mechanism of shame and the impossibility of social reintegration for survivors.
The Nashik pattern produces exactly this displacement. Victims who come forward lose jobs, face public exposure, and, in several documented cases, face family disruption.
Victims who do not come forward carry the psychological destruction privately while remaining in an environment that continues to threaten them. Both outcomes serve the same structural function as the mass rape documented in Bangladesh: the destruction of social vitality in a targeted community through the weaponization of sexual violence.
The Continuous Thread: 1971 to 2026
The scholarly and historical case for describing what is happening to Hindus as a continuing genocide requires establishing that the events are not isolated but represent stages of a continuous plan targeting the same group with the same ideological framing and the same civilizational objective across time.
The evidence for this continuity is extensive.
The 1971 genocide targeted Hindus specifically, using sexual violence, forced conversion, physical extermination, and the destruction of temples and cultural institutions as simultaneous instruments. This matches the Lemkin definition of genocide as a coordinated plan attacking multiple foundations of group life.
The post-partition trajectory of Hinduism in Pakistan and the territories Pakistan has influenced since 1947 shows continuous application of the same pattern.
The Hindu population of West Pakistan at the time of partition was approximately 15 percent.
Today, it is less than 2 percent. This demographic elimination was achieved through targeted violence, forced conversion, abduction of Hindu women, and legal discrimination, creating conditions that made Hindu life impossible. This is Lemkin's genocide in slow motion, across decades.
The same trajectory is observable in Bangladesh since partition, accelerating after 1971 and again after the fall of the Hasina government in 2024. The Hindu population of East Pakistan at the time of partition was approximately 28 percent. Today it is under 8 percent. Every decade shows the same instruments in operation: temple destruction, forced conversion, abduction of Hindu women, land seizure, and periodic mass violence.
Bay of Blood also does not tell the full story of Operation Searchlight. It glosses over the massacres of minority Hindus by Yahya Khan's army and paramilitary collaborators in East Pakistan, a tragedy that echoes even today with rising Islamic fundamentalism and ongoing attacks on minorities.
In India, the same ideological apparatus that produced Operation Searchlight operates through different delivery mechanisms.
- It operates through organized grooming networks in Kerala, documented by NIA investigations that established ISIS financial links.
- It operates through conversion rackets documented from Uttar Pradesh to Karnataka.
- It operates through the Ajmer Sharif scandal of the 1990s, which established that organized sexual targeting of Hindu women by networks with religious ideological framing predates the current moment by decades.
- And now it operates through corporate infiltration in India's IT sector, as documented in Nashik, with central agency involvement confirming foreign coordination.
The target throughout all of these events, across 75 years and multiple national boundaries, is the same:
What "Continuing Genocide" Means for Hindus in the Indian Subcontinent
The claim that what Hindus face constitutes a continuing genocide is not a rhetorical escalation. It is a specific analytical claim with specific scholarly content.
Raphael Lemkin, whose Axis Rule in Occupied Europe defined genocide before the 1948 Convention codified it, understood genocide as a process unfolding across time through multiple techniques, not a single event. He explicitly recognized biological, cultural, social, economic, religious, and moral techniques of genocide, all of which can operate simultaneously and which need not terminate in mass killing to constitute genocide. His framework explicitly allows for the recognition of genocide-in-progress, which was his entire motivation for developing the concept: to enable intervention before annihilation was complete.
Applying the Lemkin framework to the Hindu experience across the subcontinent from 1947 to 2026 produces the following assessment.
The political technique is documented: systematic disenfranchisement and constitutional discrimination against Hindus in Pakistan and Bangladesh, combined with a political-ideological infrastructure that generates and sustains anti-Hindu targeting within India itself.
The social technique is documented: the destruction of Hindu social institutions, temples, and cultural infrastructure across Pakistan and Bangladesh, combined with organized social exclusion through grooming and conversion operations within India.
The biological technique is documented: the forced conversion, abduction, and impregnation of Hindu women across Pakistan and Bangladesh since 1947, and the organized corporate grooming operations within India that target Hindu women's reproductive autonomy through psychological manipulation and sexual exploitation.
The economic technique is documented: the destruction of Hindu economic life through land seizure and legal discrimination in Pakistan and Bangladesh, and the targeting of India's economically critical IT sector through organized corporate infiltration designed to destroy the sector's credibility and Hindu workers' safe participation in it.
The religious technique is documented: the systematic destruction of Hindu temples and sacred sites across Pakistan and Bangladesh, combined with the forced religious humiliation of Hindu employees in Nashik as a precondition for sexual exploitation.
The moral technique is documented: the construction and sustained maintenance of an ideological framework that frames Hindus as impure, subhuman contamination in an Islamic civilizational space, requiring either conversion, subjugation, or elimination.
This is the definition of a continuing genocide.
It does not require mass killing at every moment. It requires the sustained, coordinated deployment of multiple techniques aimed at destroying the foundations of Hindu group life.
The Analytical Consequence: What Must Follow
The analytical consequence of recognizing the TCS Nashik case as a stage in a continuing genocide, rather than as a workplace misconduct incident or even as a national security threat in the narrower sense, is that the appropriate response framework changes completely.
Workplace regulations, sexual harassment law, and corporate governance reforms address workplace misconduct. Counter-terrorism law and NIA investigations address national security threats. The legal and institutional framework that addresses genocide is entirely different, and India does not currently have domestic legislation that applies it to the organized targeting of Hindu women within Indian territory.
The scholarly framework established here, Sharlach's rape-as-genocide analysis, the Card and Allen framework of social death as the genocidal mechanism, and the Fisher legal analysis of forced impregnation as a Genocide Convention violation, collectively provide the intellectual architecture for exactly the legal and institutional response India needs.
The connecting thread is not coincidental. It is ideological, organizational, and continuous.
Recognizing it as such is not alarmism. It is the minimum analytical honesty that the evidence, the scholarship, and the 75-year civilizational record demand.
The Nashik case is not an isolated corporate corruption story.
It is the most recent documented instance of an organized genocidal process that has been operating against Hindus for 75 years, across three countries, using every technique that Lemkin identified as genocidal, adapting its delivery mechanisms to each era's institutional landscape, and consistently targeting the same group, through the same ideological logic, for the same civilizational purpose.
India has the scholarship to name this correctly.
There is a legal tradition for responding to it appropriately.
What it has consistently lacked is the institutional will to apply the framework that the facts demand.
So long as every instance of organized anti-Hindu targeting is processed through the communal relations frame rather than the genocide frame, the response will always be calibrated to community harmony rather than group survival.
And a response calibrated to harmony while a genocide is in motion is, in its functional consequences, a form of complicity.
The Economic Warfare Dimension
The single most important intellectual shift India needs to make about the TCS Nashik case is this: it must stop being treated as a story about religious harmony or communal relations.
Every time the discourse defaults to secularism, love jihad politics, or Hindu-Muslim tensions, the operational reality gets obscured.
India's IT sector is on track to cross $300 billion in revenue by FY2026 and reach $350 billion by 2030. Its workforce will reach 7.5 million by 2030. It employs the largest fraction of India's educated professional youth. It earns more foreign exchange than any other sector.
It is the primary mechanism by which India has built credibility in the global technology economy over the past three decades.
India's IT sector is the primary engine of its formal economy, foreign exchange earnings, global standing, and the conversion of its demographic dividend.
India's IT-ITeS engine continues to show resilience despite global geopolitical disturbances. This is its critical importance.

If a network of organized grooming and conversion operations is running across this sector, as the Nashik case and the reported pattern across Hyderabad, Pune, Kolkata, and Mumbai suggest, the implications extend well beyond individual victims.
- Workforce attrition is the first economic consequence. Victims who leave jobs due to harassment remove themselves from the productive workforce. Multiple victims in Nashik left TCS before the case surfaced. Scaled across a sector employing millions, this constitutes a systematic drain on Hindu intellectual and professional capital.
- Psychological warfare against participation is the second consequence. If Hindu families in tier-2 cities, where IT sector employment represents the primary pathway to middle-class entry, come to associate IT employment with danger for their daughters, the chilling effect on workforce participation could be substantial and persistent.
- Trust erosion in institutions is the third consequence. The TCS case has already shaken faith in India's most prestigious IT brand as a safe employer. The expansion of IT operations into tier-2 and tier-3 cities adds another layer. Firms are no longer concentrated in Bengaluru, Hyderabad, or Mumbai. Centers such as Nashik reflect this shift. Corporate policies are designed centrally but implemented locally. (Source: IT sector still struggles with gender imbalance / Policy Circle) The decentralization of IT to tier-2 cities, which is economically valuable, simultaneously creates enforcement gaps that organized networks can exploit precisely because central oversight does not automatically translate into local enforcement.
- Data and IP access are the fourth and most alarming consequence. An organized network embedded in India's IT sector is simultaneously an intelligence threat. IT employees have access to client data, government systems, financial infrastructure, and defense-adjacent technology companies. Converted or compromised employees with controlled bank accounts and blackmail exposure represent a potential ISI intelligence asset. The NIA's involvement in the Nashik investigation reflects institutional recognition of exactly this threat dimension.
Let us look at the full spectrum of risk that TCS and, indeed, India, its citizens, and even the clients are being subjected to.
TCS Is Not Just an IT Company: The Critical Infrastructure Dimension
The analysis of the Nashik case becomes qualitatively more alarming the moment you understand what TCS actually does beyond writing enterprise software and managing BPO operations.
One of its divisions, TCS iON, provides scalable infrastructure for national-level examinations such as JEE and NEET in India, offering adaptive learning tools for personalized assessments and advanced analytics that provide actionable insights for both students and institutions.
ION Digital Zone is a technology-enabled exam center set up by TCS iON to conduct large-scale, secure, and standardized online exams. There are 300-plus IDZs located in almost every Indian state and union territory. IDZs are used by almost every major government, private, and university-level exam body.
TCS iON operates a state-of-the-art Command Center at its Sholinganallur facility with features including monitoring the exam process through a set of over 150 parameters to prevent, predict and manage incidents, tracking the movement and the devices carried by every candidate at any exam center via a live CCTV feed, predicting the readiness of the center based on past incidents and the current live feed of events in the exam center, and issuing alerts about any malpractice attempts based on the learnings from the malpractice patterns of the past.
TCS iON holds the question papers for JEE Main, NEET, GATE, CAT, AIIMS, IBPS, SBI banking exams, and SSC. These are the gateway examinations that determine who enters India's engineering colleges, medical schools, banks, and civil services.
The data infrastructure for these tests, the anti-cheating algorithms, the biometric verification systems, the encryption keys, the exam center networks across 300 plus locations spanning every Indian state, and the live CCTV feeds from exam centers are all administered through TCS iON systems.
An organization whose Nashik BPO unit was penetrated and operated for four years by a network with documented foreign coordination, which produced blackmail material, controlled bank accounts of compromised employees, suppressed internal complaints through a captured HR apparatus, and maintained external handler contact with a Malaysia-based preacher, is the same organization that holds the keys to India's most consequential national examinations.
The question is how anyone can confidently assert that it is not, given what the Nashik case has revealed about TCS's internal security culture.
Why are we saying this?
Intelligence Operations can use various infiltrated spaces to create a collective objective aimed at a particular target.
A recent report claims that the iON TCS platform was compromised, resulting in the leak of multiple details about the JEE Mains exam.
The Central Bureau of Investigation has launched an investigation, hoping to quickly find information about the perpetrators of the attack.
TCS iON is the most important provider of exam services in India.
The intelligence agency is also investigating several TCS iON labs at various locations where the tests were conducted, including the local Sonipat University. The anomalies began to be detected in the first days of September, which coincides perfectly with the application dates of the JEE Mains exam.
That CBI investigation in 2021 established that the TCS iON platform had been compromised in relation to JEE Main.
At that time, the investigation focused on criminal cheating networks.
This is not a conspiracy hypothesis. It is a straightforward logical implication of the Nashik evidence.
The Data Access Map: Understanding What Was Within Reach
The Nashik unit was a BPO operation. BPO employees in major Indian IT companies operate across business lines, serve multiple clients, have access to internal networks, and, in many cases, handle data that crosses into sensitive client territory. To understand the full intelligence value of having compromised assets inside TCS, consider the breadth of TCS's actual client and government relationships.
TCS has won a multi-million-pound, multi-year contract from the Home Office, a key department of the United Kingdom government, to manage the technology needs and support services for the newly formed Disclosure and Barring Service.

TCS's engagement with the UK public sector market over recent years has included participation in multiple technology-enabled transformation programs. Key government clients in the UK include National Employment Savings Trust, Cardiff City Council, Child Maintenance Group, and The Big Lottery Fund.
TCS provides services to the Department of Work and Pensions, pension provider Nest, the Department for Education, the BBC, and Cardiff City Council. There were also security concerns regarding public-sector data residing in Indian data centers.

TCS will help develop advanced security protocols to protect critical infrastructure and leverage the TCS Cyber Defense Suite, offering cyber intelligence, resilience, vendor risk management, and identity security for the Philippine government. The citizen-centric services will include services in areas such as digital private infrastructure, healthcare, and digital banking.
An organized network that successfully placed assets inside TCS and kept them there for four years, with external handler coordination and documented suppression of internal complaints, had potential access to a data universe of extraordinary sensitivity.
Financial data. Government citizen data. Healthcare records. Banking infrastructure blueprints. Cybersecurity architectures. National examination systems.
The individuals who were sexually harassing and raping Hindu women in Nashik may not have been operating at the senior enough technical levels where this data would be directly accessible.
But that would be a horribly inaccurate analytical frame to employ here.
Organized intelligence operations use foot soldiers to compromise and control individuals at lower access levels, who then become assets that can be leveraged upward.
A compromised employee who becomes financially controlled, blackmailed, and ideologically converted is a recruitment asset for the next tier of penetration.
AI and Geopolitics Pressures on the Indian Economy's Cash Cow - the IT Sector
Nashik case comes up against the backdrop of AI disruption and geopolitical pressure on the Indian IT sector.
India's IT sector is under the most severe structural pressure it has faced since its formation.
- AI-driven automation is compressing demand for traditional IT services.
- US immigration and visa policy creates unpredictable constraints on workforce deployment.
- Nearshoring trends in Europe and North America are reducing some outsourcing advantages.
Margin pressure is intensifying as clients demand more for less. The sector is in the middle of a forced transformation that requires it to move up the value chain faster than it ever has before.
Trust.
The belief among Western governments, multinational corporations, financial institutions, and sovereign entities is that Indian IT companies can be trusted with sensitive data, critical infrastructure, and government systems.
That credibility is not some abstract notion. It is the product of three decades of demonstrated reliability and the foundation on which every future contract, every government partnership, and every capability expansion is built.
There were also security concerns regarding public-sector data residing in Indian data centers.
This single sentence from a UK technology analysis piece encapsulates the pre-existing vulnerability.
Western governments have always had latent concerns about outsourcing sensitive operations to Indian IT firms. Those concerns have been managed and overcome through TCS's demonstrated track record, its growing on-shore presence in client countries, and its security certifications and compliance frameworks.
The Nashik case hands every adversary of India's IT sector the single most powerful narrative weapon they could possibly have:
That narrative, properly weaponized by India's competitors in the global IT services market, can undo the accumulated credibility of thirty years in ways that no recession, no regulatory change, and no technology disruption could achieve as efficiently.
The Question Western Governments and Corporations Will Now Ask
Every Western government contracting officer, every CISO at a global bank, every procurement committee at a Fortune 500 company that uses Indian IT services will now be asking the same question. If this happened at TCS, one of the largest, most professionally managed, most globally certified IT companies in the world, what is happening at the others?
The TCS Nashik row has triggered claims from across the IT industry in India, as Tech Mahindra and Infosys deny the allegations and reiterate their zero-tolerance policies. Which is neither here nor there.
After all, what is the value of such self-produced denials?

The fact that other companies are now in defensive denial mode confirms that the question is already being asked across the sector.
These companies and their administrations, along with the boards, have to get one thing clearly - Denial is not reassurance.
The UK Home Office holds TCS's contract for the Disclosure and Barring Service, which processes criminal record checks for individuals working with children and vulnerable adults. The UK Department of Work and Pensions uses TCS for pension administration. The Department for Education uses TCS for educational data management. The BBC outsources IT to TCS. Scotland's pension system has migrated millions of accounts to TCS platforms.
- How many of these clients will now be conducting formal security reviews of their TCS partnerships?
- How many will be demanding audits of TCS's internal security culture and insider threat detection capabilities?
- How many will question whether their sensitive data has been, or could be, compromised by organized networks of the kind that operated undetected in Nashik for four years?
The Conversion Pipeline as an Intelligence Preparation Architecture
The analytical link between the conversion operations in Nashik and potential intelligence exploitation requires explicit elaboration, because it is being underweighted in public discourse.
The Nashik operation's documented architecture, financial control of bank accounts, blackmail material production, sexual exploitation, psychological manipulation designed to separate victims from family networks, and introduction to a foreign handler via video call, maps precisely onto the preparation architecture for intelligence asset development.
Every element serves a dual purpose.
Financial control via bank account manipulation serves grooming and religious conversion. It also serves asset control in an intelligence context. A converted employee whose finances are managed by the network has both religious and operational dependency on that network.
Blackmail material production serves the suppression of victim complaints.
It also serves coercive asset recruitment. A compromised employee who cannot report what happened without exposing themselves to blackmail is a candidate for demands to provide access, information, or facilitation.
Separation from family networks serves the isolation that enables psychological manipulation. It also eliminates the external support structure that might prompt an asset to report, seek help, or break contact with the network.
Introduction to a Malaysia-based handler serves the religious conversion pipeline. It also establishes a foreign contact and communication channel that, in an intelligence context, represents exactly the offshore handler relationship that ISI's hybrid espionage model relies upon.
It requires only the recognition that the operational architecture the Nashik network built is functionally identical to the intelligence asset preparation architecture, and that even if the primary purpose was religious, the secondary intelligence-exploitation potential was inherent in the structure and would have been visible to any external handler with intelligence tradecraft experience.
The Credibility Destruction as the Primary Strategic Objective
Here is the most disturbing strategic interpretation of what the Nashik operation represents, and it requires stating directly. Regardless of whether data was actually extracted or assets were actually recruited for intelligence purposes, exposing the operation itself achieves a strategic objective of enormous value.
The revelation that TCS, India's most prestigious IT company, can be penetrated by an organized, foreign-directed network for four years without detection destroys confidence in Indian IT security more effectively than any cyberattack could.
You see, a cyberattack can be patched.
Security certifications can be reissued. Compliance frameworks can be updated.
The narrative that Indian IT companies are penetrated from within by organized religious networks with foreign handler connections cannot be managed with a software update.
The destruction of credibility is itself the weapon. Whether or not the Nashik network successfully extracted data or converted employees into intelligence assets, the fact of its existence and its four-year operational success demonstrates a structural vulnerability in Indian IT security culture that no Western government or corporation can rationally ignore.
This is economic warfare through reputational destruction, and it is more sophisticated and more durable in its effects than any kinetic or cyber attack could achieve.
The Counter-Strategy India Needs
The strategic counter-response must operate simultaneously at five levels.
- Level 1: Immediate Sectoral Security Audit: The NIA investigation must not be confined to TCS Nashik. It must be expanded into a formal audit of the internal security culture, hiring practices, complaint-suppression records, and foreign-contact histories across all major Indian IT companies that operate critical national infrastructure. TCS iON's examination systems must undergo an immediate independent security audit, with specific attention to insider threat detection capabilities and any anomalous access patterns over the past four years.
- Level 2: Legislative Action: India needs immediate legislation classifying the organized infiltration of critical digital infrastructure by foreign-directed networks as a national security offense, with penalties equivalent to those under espionage statutes. The current legal framework prosecutes individuals for sexual harassment and conversion. It does not have adequate provision for the organized, foreign-coordinated, multi-year infiltration of critical IT infrastructure. That legislative gap must be closed urgently.
- Level 3: International Communication: India needs to communicate proactively and credibly with its major IT sector clients and partner governments before those governments conduct their own assessments and reach their own conclusions. A proactive communication that acknowledges the threat, describes the response, and demonstrates the structural changes being implemented is infinitely better than reactive denial when Western security services begin their own reviews. India's National Cybersecurity Coordinator and the Ministry of Electronics and Information Technology need to engage directly with the UK, US, and EU cybersecurity authorities on this issue.
- Level 4: The Malaysia Question: The documented trajectory from TCS Nashik to a Malaysia-based handler is a diplomatic issue requiring formal action. India should formally raise with Malaysia the evidence that a Malaysian-resident Islamic preacher was used as an external coordination node in an organized infiltration operation targeting Hindu employees of a critical infrastructure company in India. Malaysia's consistent protection of India-designated individuals and its documented role as a financial transit node for ISI-linked operations targeting India, as evidenced by the $117,000 fund transfer through Saudi Arabia and Malaysia for the JMB radicalization operation, constitute a pattern requiring formal diplomatic consequences rather than bilateral politeness.
In January 2020, a report by The Times of India revealed that Indian security agencies had warned their armed forces and border patrols about ISI training 40 Rohingya individuals in Cox’s Bazar. The report stated that this training was being carried out via the Jamaat-ul Mujahideen Bangladesh (JMB), a Bangladeshi terrorist organization. ISI allegedly provided JMB with an initial installment of 10 million Bangladeshi Taka (approximately US$117,000), funneled through Saudi Arabia and Malaysia. (Source: Tehran’s subversive agenda: Radicalizing Rohingyas to target Saudi Arabia / Weekly Blitz)
- Level 5: Civilizational Reframing: India's public discourse and its institutional response must both be reframed around the correct analytical category. The TCS Nashik case is a national security event that weaponizes religious targeting as an entry technique for organizational infiltration of critical economic and examination infrastructure. Treating it as a communal relations issue enables the perpetrators' framing, diminishes the severity of the institutional response required, and prevents the comprehensive counter-architecture that the threat actually demands.
The young Hindu men and women who go to work every day in India's IT companies, in Nashik and Pune and Hyderabad and Bengaluru and every tier-2 city where TCS and Infosys and Wipro and Tech Mahindra have planted their operations, deserve to work in an environment that takes their security seriously as a national obligation.
We have to remember one thing clearly - Individual outrage, however morally appropriate, does not constitute a security strategy.
The four-year silence inside TCS Nashik cannot and should not be treated as a failure of information.
It was most clearly a failure of institutional will.
Repairing that requires building systems whose default setting is protection rather than suppression, and whose accountability flows upward to boards and national agencies rather than terminating with a captured HR department in a tier-2 city office.









