In India, the administration of high-stakes examinations is a matter of profound socio-economic significance. Today, let us understand how they are administered under the new framework and why the institutional weaknesses exposed by the recent TCS Nashik Grooming scandal within Tata Consultancy Services have parallels to cases in which the integrity of TCS iON's most important admission examinations has been compromised.
The Digitalization of High-Stakes Assessments and Emerging Threat Vectors
The paradigm shift from localized, analog pedagogical assessments to decentralized, synchronous computer-based testing (CBT) networks was predicated upon a fundamental hypothesis: that algorithmic delivery and digital cryptographic barriers would inherently neutralize the human vulnerabilities associated with physical paper leaks.
The National Testing Agency (NTA), established as an autonomous testing organization, was entrusted by the Government of India with the monumental task of conducting free, fair, and transparent examinations for admission to premier higher education institutions.
Among these crucial assessments, the Joint Entrance Examination (Main) is one of the most competitive gateways to undergraduate engineering programs (B.E./B.Tech) at elite institutions such as the Indian Institutes of Technology (IITs) and the National Institutes of Technology (NITs).
To manage the immense scale and complexity of these national examinations, educational authorities frequently partner with major corporate technology conglomerates to utilize secure testing platforms.
Solutions such as the digital assessment platforms provided by Tata Consultancy Services (TCS), including the ubiquitous TCS iON platform and associated specialized software architectures like iLeon, are deployed nationwide to ensure end-to-end encryption, biometric verification, and secure test delivery.
These corporate partnerships are designed to leverage private-sector cybersecurity expertise to protect the integrity of the state's educational meritocracy.
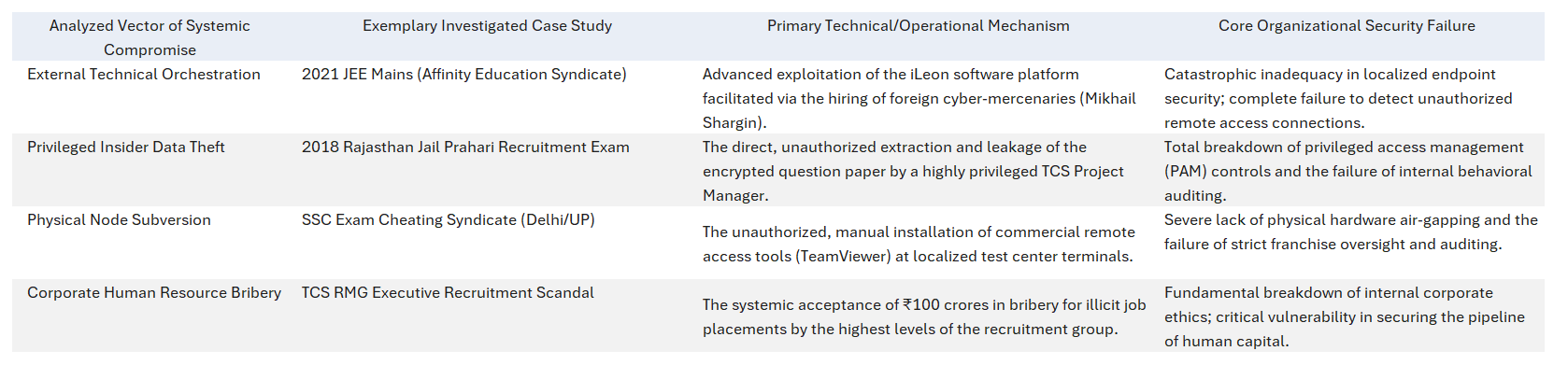
However, the digitalization of the examination ecosystem has not eradicated academic fraud; rather, it has catalyzed the evolution of highly sophisticated, digitally enabled academic cybercrime.
In this report, we provide an exhaustive, multidimensional analysis of the systematic compromise of digital examination platforms.
It explicitly addresses the breach orchestrated by a Noida-based educational entity whose directors were arrested for subverting these critical platforms.
By examining the structural vulnerabilities of testing software, the internal corporate instability within technology providers, and the socio-legal ramifications of these breaches, this analysis aims to deconstruct the anatomy of modern testing compromises and to offer strategic frameworks for ecosystem remediation.
Deconstructing the Noida-Based Syndicate: Organizational Structure and Key Actors
The 2021 JEE Mains examination manipulation case represents a watershed moment in the history of Indian educational cybercrime, illustrating how criminal enterprises co-opt corporate structures to execute nationwide digital fraud.
At the epicenter of this highly organized operation was a corporate entity operating under the guise of an international educational consultancy, that systematically targeted the digital assessment infrastructure utilized for the engineering entrance exams.
Identification of the Entity and Its Directorship
The primary query under investigation concerns the specific individuals responsible for orchestrating the compromise of the testing platforms from their base in the National Capital Region.
The Central Bureau of Investigation (CBI), India's premier investigative agency, successfully identified M/s Affinity Education Private Limited as the prime accused organization driving the manipulation of the testing platforms.
Headquartered in Noida, Gautam Budh Nagar, Uttar Pradesh, the company projected a highly sophisticated corporate facade, presenting itself as a legitimate facilitator of domestic and international higher education.
The investigation explicitly identified the three principal directors and signatories of Affinity Education Private Limited who masterminded the compromise of the examination ecosystem.

These three directors, whose arrests marked a critical victory for law enforcement, are:
- Siddharth Krishna
- Vishwambhar Mani Tripathi (frequently referenced in legal documentation as Vishambhar Mani Tripathi or V. Mani Tripathi)
- Govind Varshney (also documented in court records as Govind Vaarshney)
These three individuals served as the strategic architects of the syndicate.
They leveraged their corporate infrastructure to solicit desperate clients, launder massive sums of illicit funds, and coordinate with advanced technical operators to breach the testing software architectures, including the iLeon platform deployed for the 2021 assessments.
The Illusion of Legitimacy and Subsidiary Network
Affinity Education did not operate as a clandestine, underground ring. Interestingly, it functioned in plain sight within the Noida corporate ecosystem. The entity claimed on its official website to maintain partnerships or "tie-ups" with over 650 universities globally, providing a veneer of corporate legitimacy that masked its illicit core operations.
This illusion of legitimacy was critical to their operational model, as it allowed them to openly recruit clients under the guise of providing standard admission counseling services.
The three directors established a structured hierarchy of employees who functioned as admission counselors, regional coordinators, and operational fixers.
The corporate compartmentalization ensured that the directors remained insulated from the immediate, ground-level technical execution of the hacks. The CBI apprehended several key employees and associates who played critical roles in executing the scheme.
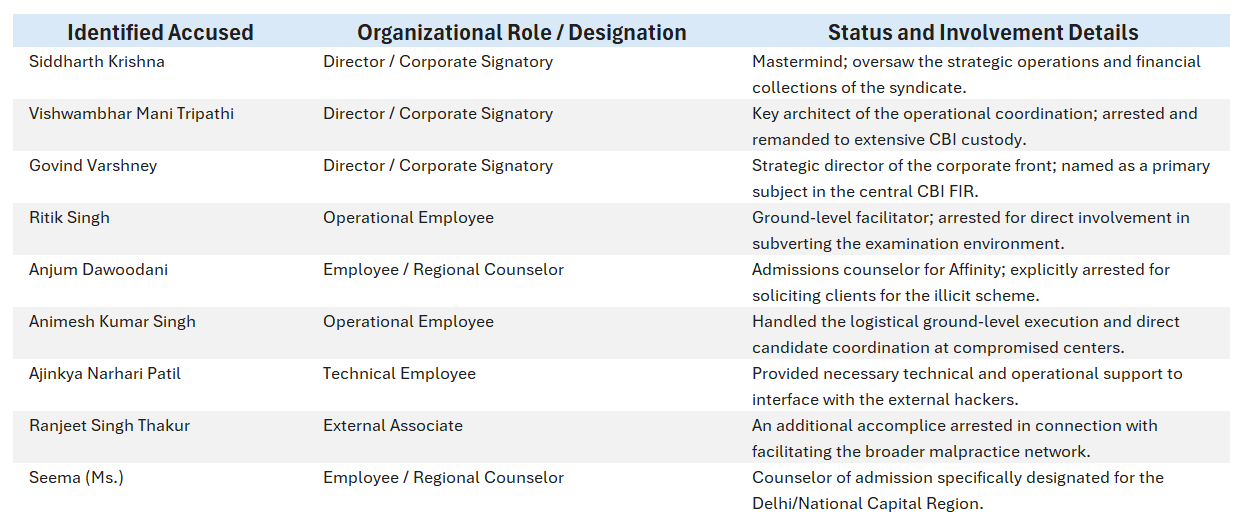
The most shocking aspect was the sheer professionalism of the whole set up.
By separating the counseling division (which lured the clients), the financial division (which extorted the funds), and the technical hacking division (which executed the software breach), the three directors created a resilient, decentralized fraud network that required an unprecedented multi-agency response to dismantle.
The Financial Architecture and Psychological Coercion of the Scam
The subversion of the digital testing platforms was not merely a technical endeavor; it was an immensely lucrative financial enterprise built upon the systematic psychological coercion of students and their families. The fourth session of the JEE (Mains) 2021 Computer Based Test (CBT), conducted across August 26, 27, 31, and September 1 and 2, served as the primary operational window for this extortion.
Sitting in a distant location from examination centres, a group of “solvers” hacked into computers and wrote the exam for engineering candidates, while the actual candidates scribbled on sheets, pretending to be making calculations and solving questions. This is how the fourth session of the competitive Joint Entrance Exam (JEE), meant for admission to top engineering colleges, was allegedly manipulated in the last two weeks by a Kanpur-based private company, Affinity Education Pvt. Ltd, to facilitate admissions to a few students. On 1 September, the Central Bureau of Investigation (CBI) registered a case to investigate the “irregularities” in the exam, after the agency received information on the ongoing racket and booked the company’s directors, consultants, technicians and touts in the case. Eleven people have been arrested so far. (Source: This is how JEE Mains was ‘manipulated’: ‘Solvers’ hacked into computers to write papers / The Print)
The Economics of Academic Subversion
The financial model engineered by Siddharth Krishna, Vishwambhar Mani Tripathi, and Govind Varshney was highly predatory, capitalizing on the intense socio-economic pressure surrounding higher education in India.
The directors and their network of counselors, such as Anjum Dawoodani and Ms. Seema, targeted desperate candidates, demanding exorbitant sums ranging from ₹12 lakh to ₹15 lakh per candidate. In exchange for this massive fee, the syndicate guaranteed to artificially inflate the candidates' examination percentiles, thereby assuring their admission into prestigious, state-funded National Institutes of Technology (NITs).
Collateralization of Human Capital
A critical vulnerability in illicit transactional models is the risk of client default post-service delivery. Because the syndicate could not rely on legal contracts to enforce the payment of the ₹12-15 lakh fees after the candidate successfully cleared the exam, they implemented a draconian system of physical collateral.
The syndicate coerced the candidates into physically surrendering their most vital, irreplaceable life documents. This included the confiscation of their original Xth (10th) and XIIth (12th) grade educational mark sheets.
Furthermore, the network seized the students' official NTA user IDs, digital passwords, and heavily capitalized post-dated cheques (PDCs).
These critical documents and financial instruments were strictly held hostage within the company's Noida headquarters. The operational mandate dictated that these materials would only be released back to the candidates after the illicit admissions were finalized and the massive cash commissions were fully realized and cleared into the syndicate's shadow accounts.
This methodology represents a profound escalation from simple bribery to systematic psychological hostage-taking. The retention of original educational certificates essentially paralyzed the candidates, ensuring their absolute silence and compliance, while simultaneously shielding the Affinity Education directors from internal exposure or whistleblower threats from disgruntled clients.
Anatomy of the Technical Subversion: Exploiting the Ecosystem
While the financial transactions and corporate planning took place within the opulent confines of the Noida headquarters, the actual execution of the technical hack was strategically decentralized. The syndicate exploited deep geographical and infrastructural vulnerabilities inherent in the NTA's franchised testing network to bypass the assessment software's cryptographic protections.
The Vulnerability of Franchise Test Centers
The NTA and corporate partners like TCS operate at a scale that necessitates the franchising of physical testing locations.
The Affinity Education network established a corrupt nexus with a specific examination center situated in Sonepat, Haryana.
By compromising the local administrative staff or IT administrators at this specific node, the syndicate was able to bypass the foundational requirement of hardware air-gapping.
Bypassing Application Whitelisting via Remote Access
The primary technical mechanism used to subvert the CBT was the illicit deployment of remote-access tools.
Secure testing software is theoretically designed to lock down the operating system, preventing the candidate from opening web browsers, accessing local files, or utilizing secondary applications. However, the Affinity syndicate successfully manipulated the online examination by allowing external, highly skilled "solvers" to view the live screens and answer the complex technical question papers on behalf of the candidates seated inside the Sonepat center.
This implies a catastrophic failure of the localized endpoint detection and response (EDR) mechanisms.
For an external solver to take control of the mouse and keyboard inputs remotely, the compromised center's network must have permitted virtual network computing (VNC) or remote desktop protocols (RDP) to bypass the platform's anti-cheat mechanisms.
The systemic nature of this vulnerability is corroborated by parallel investigations into allied testing environments.
In a structurally identical joint operation, the Delhi and Uttar Pradesh Police apprehended a separate cohort of four individuals—Ajay, Parma, Gaurav, and Sonu—from the Gandhi Nagar area.
This parallel syndicate was charging candidates ₹15 lakhs to facilitate cheating in the Staff Selection Commission (SSC) online examinations.
Their primary technical tool was identified as "TeamViewer," a widely available, legitimate commercial remote access application.
The repeated, successful use of tools such as TeamViewer or customized remote access trojans (RATs) against these supposedly secure platforms indicates a chronic, ecosystem-wide failure to maintain application whitelisting at localized franchise testing centers. When hardware tampering becomes trivial due to compromised local staff, the software-layer security provided by entities like TCS or NTA is rendered entirely moot.
Transnational Cyber-Mercenaries and the iLeon Hack
The specific software architecture targeted by the Affinity Education syndicate during the 2021 JEE Mains was identified as iLeon, a robust platform utilized to deploy the high-stakes assessment.
The compromise of a specialized, enterprise-grade platform like iLeon required advanced technical capabilities that vastly exceeded the internal IT competencies of the three corporate directors in Noida.
To execute the breach, the syndicate engaged transnational cyber-mercenaries, highlighting the globalization of domestic academic fraud. The overarching domestic technical operation was reportedly masterminded by Vinay Dahiya, who acted as the technical bridge between the corporate directors and the dark web.
Dahiya was subsequently tracked to an operational hideout in Gurugram and arrested by the CBI in March 2023, and he was remanded to five days of CBI custody by a special court.
Also Read - Russian "Hacker" Who Manipulated Joint Entrance Exam Last Year Gets Bail / NDTV
Shargin's involvement underscores a terrifying evolution in the threat landscape: domestic educational fraud syndicates are now actively leveraging international Cybercrime-as-a-Service (CaaS) marketplaces to hire elite specialists capable of cracking proprietary government and corporate assessment software.
The deployment of a Russian hacker to manipulate an Indian engineering entrance exam demonstrates that testing infrastructure must now be defended against nation-state-level offensive cyber capabilities.
The Insider Threat Matrix: Corporate Personnel Vulnerabilities
The breach orchestrated by Affinity Education, while relying on external hackers, cannot be viewed in isolation from the broader vulnerabilities plaguing the corporate entities that build and manage these testing platforms. A critical analysis of the ecosystem reveals that the most devastating threats often originate from within the very corporations contracted to secure the data. The phenomenon of insider complicity poses an existential threat to the validity of the testing ecosystem.
The Rajasthan Jail Prahari Exam Leak
Even the most robust zero-trust architectures can be entirely subverted by authorized personnel operating with malicious intent. A parallel investigation conducted by the Rajasthan Police’s Special Operations Group (SOG) into the 2018 Jail Prahari (Warder) Recruitment Exam provides a harrowing case study of this vector.
The SOG explicitly determined that the examination question papers were leaked directly from the source by an internal employee of Tata Consultancy Services (TCS), the exact corporate entity contracted by Sardar Patel University in Jodhpur to conduct the secure assessment.
The mastermind of this catastrophic data hemorrhage was identified as Jagjit Singh, a highly placed TCS Project Manager based in Gurugram, who previously resided in Noida.
The illicit materials were then brokered into the shadow economy by a middleman, Sandeep Kandiyan, a resident of Sonipat, Haryana.
Kandiyan negotiated a massive ₹60 lakh payoff to distribute the leaked answer keys to paying candidates.
Based on intelligence gathered during Kandiyan's interrogation, the SOG detained and arrested Karan Kumar in Dehradun on March 23, followed by the arrest of the TCS Project Manager, Jagjit Singh.
The geographical overlap between these distinct syndicates is striking. The TCS insider leak flowed through Noida, Gurugram, and Sonipat—the exact same regional triangle utilized by the Affinity Education directors to execute the JEE Mains hack.
Systemic Corporate Governance Failures and Ethical Decay
The integrity of high-stakes digital platforms is inextricably linked to the corporate governance, ethical hygiene, and internal stability of the organizations that develop and manage them.
When a massive technology conglomerate is entrusted with the digital future of millions of students, any internal breakdown in corporate ethics directly degrades the security posture of its deployed products. Recent unprecedented controversies surrounding major IT providers reveal profound systemic vulnerabilities that foster environments highly conducive to malicious exploitation.
The ₹100 Crore Recruitment Bribery Network
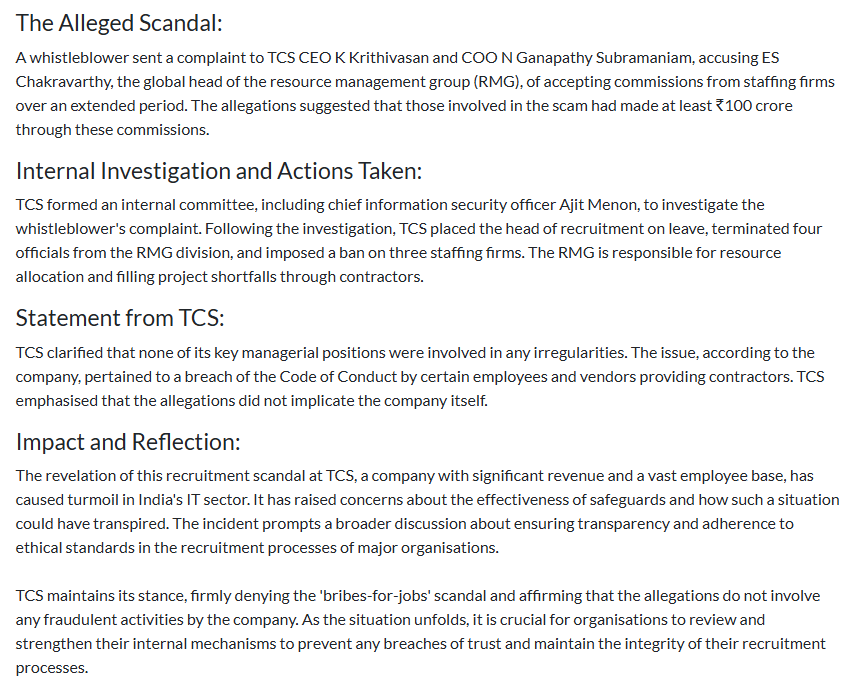
An in-depth analysis of internal corporate stability reveals that critical vulnerabilities frequently extend far beyond software code and deeply into the human resource management layer.

TCS recently faced a severe internal scandal that fundamentally challenged its governance models and exposed deep-seated corruption within its hiring apparatus.
The global head of the RMG, E.S. Chakravarthy, a formerly highly respected Vice President, and several other high-ranking executives responsible for crucial global hiring decisions were implicated in accepting illicit, under-the-table commissions from unauthorized staffing firms over several years.
The scale of this internal corporate fraud was staggering, with insiders estimating that the corrupt executives pocketed a jaw-dropping sum of at least ₹100 crores in illicit commissions directly linked to job offers and candidate placements.
Following the explosive complaint, the corporation was forced to assemble a crack investigative team, led by the Chief Information Security Officer, Ajit Menon, to unearth the truth.
The weeks of intense internal investigation culminated in a dramatic purge: TCS placed the head of recruitment on indefinite administrative leave, immediately axed four high-ranking RMG executives, banned Chakravarthy from entering the corporate premises, and blacklisted three secretive staffing firms whose identities remain shrouded in corporate secrecy.
When the human resource and recruitment apparatus is compromised by bribery, the quality and integrity of the technical talent pipeline are poisoned. If corporate executives are willing to accept ₹100 crores to hire unqualified or compromised engineers, the probability of inadvertently hiring malicious actors, such as project managers willing to leak examination data (like Jagjit Singh), increases exponentially.
A compromised hiring pipeline is the genesis of the insider threat.
Institutional Coercion and Workforce Unrest
Further compounding the narrative of deep corporate instability are severe allegations of internal coercion and hostile workplace environments at peripheral corporate facilities.
We have seen how the investigations spearheaded by a Special Investigation Team (SIT) into the TCS BPO center in Nashik, Maharashtra, are revealing deeply troubling allegations of organized coercion, exploitation, sexual harassment, and attempted religious conversion within the localized workforce.
The controversy escalated rapidly as multiple First Information Reports (FIRs) were filed by at least nine desperate victims who reported being systematically pressured and threatened with immediate job termination if they did not comply with the radical demands of the accused.
The state police took decisive action, arresting seven individuals involved in the alleged organized exploitation module, including an HR official who was placed in police custody, while others were remanded to judicial custody.
The investigation focused heavily on key accused individuals, including Tausif Akhtar and Nida Khan.
If she indeed was a mere telemarketer, as TCS is working hard to prove, then why is this lady hiding? What role did she play and why is her arrest so critical that a battery of lawyers is working hard to block it?
The allegations against Akhtar were particularly severe; video evidence was released by a supporting staff member claiming he was physically taken to Akhtar's private residence, forced to wear a skull cap, and coerced into offering Namaz under extreme professional duress.
Interestingly, as happens in such cases, the families of the accused vehemently denied these claims, labeling them as baseless fabrications. the fact that an undercover operation has collected detailed information and forensics shows that the families are using the religion card to thwart the law from taking its course.
The Maharashtra government, represented by Devendra Fadnavis, assured the public that the entire nexus would be thoroughly investigated, leading to the formation of the SIT to probe the full extent of the activities, including highly concerning but unverified rumors of international links to grooming gangs in Malaysia.
While these cascading internal crises, the ₹100 crore recruitment bribery network in the RMG, the deeply disturbing allegations of religious coercion and harassment in the Nashik BPO, and the violent labor unrest in the Noida facilities, are seemingly disconnected from the direct technical hacking of the iLeon examination platform, they collectively paint a picture of severe systemic vulnerability.
A corporate ecosystem that is simultaneously grappling with massive internal executive fraud, severe employee exploitation, and violent labor unrest inherently lacks the operational focus, ethical foundation, and stringent, zero-defect security posture required to protect critical national infrastructure assets such as the JEE Mains testing platform from highly organized domestic and international syndicates.
Geographic Profiling: Noida as the Epicenter of Transnational Cyber-Fraud
The operational headquarters of Affinity Education Private Limited, located in Noida, is not an isolated geographic coincidence.
To understand how three corporate directors could successfully orchestrate a nationwide examination hack utilizing Russian cyber-mercenaries, one must analyze the unique socio-technical environment of the National Capital Region.
Noida, and specifically its Special Economic Zones (SEZ), has rapidly evolved into a dual-use technological hub. While it rightfully hosts the legitimate infrastructure of multinational IT conglomerates, it simultaneously, and parasitically, serves as a fertile breeding ground for some of the world's most highly sophisticated cybercrime syndicates.
The environment that enabled the directors of Affinity Education to operate is deeply intertwined with parallel cyber-criminal enterprises operating within the exact same geographical jurisdiction.
This operation was not a localized bust; it was the culmination of 18 months of groundbreaking international collaboration between the CBI, the U.K. National Crime Agency (NCA), the U.S. Federal Bureau of Investigation (FBI), and Microsoft's digital crimes unit.
The FirstIdea syndicate masqueraded as high-level technical support staff for reputed multinational tech companies.
They utilized highly advanced calling infrastructure, sophisticated malicious behavioral scripts, Voice Over Internet Protocol (VoIP) routing, and spoofed international phone numbers routed through multiple global servers to ensure absolute cross-border anonymity.
By falsely convincing foreign nationals that their personal devices were compromised by non-existent technical problems, the FirstIdea syndicate successfully extorted over £390,000 ($525,000) from more than 100 vulnerable victims in the United Kingdom alone.
The CBI raids on the three Noida locations were executed with extreme precision, meticulously timed to coincide with the waking hours and time zones of the UK victims, resulting in the astonishing detection of live, in-progress scam calls during the physical apprehension of two key operatives, including a primary partner of FirstIdea.
The glaring existence and prolonged operational success of transnational syndicates like FirstIdea within the Noida SEZ perfectly contextualizes the Affinity Education syndicate. The regional ecosystem inherently provides bad actors with immediate, unfettered access to high-speed digital infrastructure, a vast pool of technically proficient but ethically flexible IT labor, and a deeply entrenched network of shadow financial operators capable of laundering massive sums of illicit capital.
Law Enforcement Response and Complex Judicial Dynamics
The systemic breach of the 2021 JEE Mains examination triggered an unprecedented, multi-jurisdictional law enforcement response spearheaded by the Central Bureau of Investigation. The objective was not merely to arrest the localized perpetrators, but to entirely dismantle the immediate syndicate, secure highly volatile digital forensic evidence before it could be wiped, and trace the complex financial architectures supporting the nationwide fraud.
The Nationwide CBI Raids and Forensic Seizures
Acting on highly sensitive source intelligence regarding the subversion of the NTA's autonomous testing process, the CBI rapidly registered a formal First Information Report (FIR). The case, officially designated in judicial records as RC-DAI-2021-A-0032, was registered under several of the most stringent sections of the Indian Penal Code to reflect the severity of the institutional sabotage:
- Section 420 of the Indian Penal Code (IPC): Pertaining to cheating and dishonestly inducing the delivery of property (addressing the ₹12-15 lakh extortion).
- Section 467 of the IPC: Pertaining to the forgery of valuable security, wills, etc. (addressing the manipulation of the digital credentials).
- Section 120-B of the IPC: Pertaining to criminal conspiracy (addressing the coordinated nature of the syndicate).
- Section 66D of the Information Technology (IT) Act: Pertaining to the punishment for cheating by personation by utilizing computer resources (addressing the remote access solvers taking the exam on behalf of the candidates)
Following the registration of the comprehensive case against Affinity Education Pvt Ltd and its three primary directors, the CBI launched highly coordinated, simultaneous search operations across 20 distinct locations nationwide.
These raids primarily focused on compromised private engineering colleges acting as franchise centers and illicit administrative hubs operating in the shadows.
The forensic yield from these aggressive raids was substantial and legally damning. According to the official statements provided by CBI Spokesperson R.C. Joshi, the searches led to the immediate recovery of critical digital hardware and financial evidence, directly linking the corporate entity to the hacks. The seizures included:
- 25 laptop computers heavily utilized for remote access routing and operational coordination with the external solvers.
- 7 personal computers (PCs) acting as localized administrative servers.
- Over 30 post-dated cheques (PDCs) were physically extorted from the desperate families of the candidates.
- Voluminous incriminating physical documents, notably including the original, confiscated mark sheets of various students that were held as hostage collateral in the Noida offices.
Arrests, Remands, and Extended Legal Maneuvering
The immediate tactical aftermath of the nationwide raids led to the successful arrest of seven key individuals closely associated with the Affinity Education network.
This included the crucial arrests of directors Siddharth Krishna and Vishambhar Mani Tripathi, as well as their subordinate operational employees, Ritik Singh, Anjum Dawoodani, Animesh Kumar Singh, Ajinkya Narhari Patil, and the external associate, Ranjeet Singh Thakur.
To facilitate deep, uninterrupted custodial interrogation regarding the technical mechanisms of the iLeon hack and the complex financial routing of the extorted funds, at least three of the arrested accused were formally remanded to CBI custody by the courts until September 9, 2021.
The broader legal net cast by the CBI eventually captured the highly elusive technical masterminds. Vinay Dahiya, identified as the primary domestic architect of the hack, was finally apprehended in his Gurugram hideout and remanded to CBI custody for five days by a special court in March 2023.
Furthermore, the unprecedented arrest of the Russian hacker Mikhail Shargin in October 2022 powerfully demonstrated the CBI's absolute commitment to prosecuting foreign nationals who dare to violate Indian critical educational infrastructure. Shargin was presented before the Rouse Avenue Court in Delhi, with the CBI aggressively seeking an extended two-week custody period to continue interrogating him about the highly specific cryptographic vulnerabilities he successfully exploited in the iLeon software architecture.
The judicial proceedings surrounding the case also witnessed complex, protracted legal maneuvering by various associated individuals desperately attempting to evade the CBI's dragnet. For instance, an individual named Ashish filed a comprehensive application for anticipatory bail (formally documented as BAIL APPLN. 143/2022) in the High Court of Delhi.
The critical hearing, presided over by the bench of Hon'ble Mr. Justice Anoop Kumar Mendiratta on May 5, 2022, vividly highlighted the sprawling, hydra-like nature of the ongoing investigation.
During the proceedings, the CBI, aggressively represented by Special Public Prosecutor Anupam S. Sharrma, sought to continuously consolidate its massive case against the broader, decentralized network of facilitators and regional counselors who seamlessly operated under the seemingly legitimate corporate umbrella of the Noida entity.
Broader Implications for India's Educational and Technological Infrastructure
The successful arrest of the three directors of the Noida-based Affinity Education (Siddharth Krishna, Vishwambhar Mani Tripathi, and Govind Varshney) transcends the immediate parameters of a successfully prosecuted, localized cybercrime incident.
It serves as a stark, undeniable exposure of profound systemic rot festering at the dangerous intersection of India's hyper-competitive educational sector and its rapidly yet insecurely digitizing examination infrastructure.
The Unregulated Shadow Education Economy
Affinity Education Private Limited represents the absolute zenith of a highly lucrative, fundamentally unregulated "shadow education" economy. Educational consultancies operating in India often operate within a vast regulatory gray area. By aggressively claiming legitimate affiliations with hundreds of universities, these corporate entities attract immense volumes of highly sensitive student data and unregulated financial capital. However, in the absence of strict, continuous statutory auditing by educational boards, these consultancies can seamlessly pivot from providing legitimate admission counseling to orchestrating highly illegal, technologically advanced credential-inflation schemes.
The demonstrated willingness of middle-class parents to pay exorbitant sums of ₹12 lakh to ₹15 lakh, and more disturbingly, to surrender their children's vital life documents (10th and 12th original mark sheets) as illicit collateral, speaks volumes regarding the intense, almost pathological socio-economic desperation surrounding admissions into premier engineering institutions like the NITs.This massive societal desperation generates a nearly infinite illicit market capitalization, directly incentivizing organized crime syndicates to invest heavily in advanced cyber-espionage capabilities, going so far as to hire elite Russian malware developers to crack proprietary software like iLeon.
The Erosion of Institutional Trust and Meritocratic Validity
When highly touted, ostensibly secure computer-based testing platforms are repeatedly and systematically compromised through commercial remote-access tools or high-level insider data leaks, the fundamental meritocracy of the entire nation's educational system is nullified. Candidates who legitimately and honestly use digital platforms, relying on the state's promise of fairness, are unfairly outranked and displaced by individuals who secured top-tier percentiles through the financial backing of criminal syndicates. If the absolute integrity of the JEE Mains, conducted under the stringent, autonomous purview of the NTA, can be completely bypassed by a simple, unauthorized VNC connection routed from a compromised, third-tier private college center in Sonepat, the intrinsic societal and global value of the degrees issued from the resulting elite institutions is placed under severe, irreversible reputational jeopardy.
Furthermore, the repeated, undeniable involvement of platforms and personnel associated with massive tech giants highlights a catastrophic failure in the vendor risk management protocols established by government entities. Whether it is the highly sophisticated hacking of the iLeon software specifically for the JEE Mains, the devastating direct leakage of the Rajasthan Jail Prahari exams by a deeply embedded TCS insider, or the systemic reliance on vulnerable remote desktop protocols observed in the SSC exams, the pattern is clear. The wholesale outsourcing of examination execution to private corporate conglomerates does not, and legally cannot, absolve the state of its paramount responsibility to maintain an absolutely unassailable, equitable testing environment for its citizens.
Strategic Recommendations for Securing High-Stakes Assessments
The extensive, multi-agency analysis of the Affinity Education syndicate, coupled with the deeply concerning parallel compromises across the testing ecosystem, calls for an urgent, fundamental reassessment of the national digital examination architecture. To effectively mitigate the recurrence of such highly organized, technologically advanced fraud, several systemic interventions and architectural overhauls are absolutely required.
1. Mandatory Implementation of Cryptographic Zero-Trust Architectures: Assessment software platforms, encompassing widely used solutions like TCS iON and specialized architectures like iLeon, must immediately migrate to strict, unyielding Zero-Trust operational architectures. The foundational application layer must be engineered to aggressively and autonomously terminate all concurrent background processes, virtual machine environments, and commercial remote desktop protocols (such as TeamViewer, VNC, or AnyDesk) the millisecond they are detected. Furthermore, continuous, AI-driven behavioral biometric monitoring must be standardly deployed to instantly detect anomalous mouse-movement trajectories or superhuman keyboard-input speeds that definitively indicate remote human or algorithmic intervention.
2. Complete Eradication of the Private Franchise Center Model: The systemic reliance on private engineering colleges and third-party IT facilities (exemplified by the severely compromised center utilized in Sonepat, Haryana) introduces unmanageable physical security vulnerabilities into the testing chain. To ensure absolute environmental integrity, the NTA and its corporate testing partners must rapidly invest in establishing wholly-owned, permanently air-gapped regional testing fortresses. These dedicated facilities must be equipped with military-grade biometric access controls, cellular jamming technologies, and hardware-level network firewalls that physically prevent any external IP routing or local network tampering.
3. Stringent Security Vetting of Corporate IT Personnel: The insider threat remains the most difficult vector to defend against. Corporate employees of tech conglomerates who manage highly sensitive national examination data, much like the TCS project manager arrested in the devastating Rajasthan paper leak, must be subject to ongoing, high-level government security clearances akin to those required to manage critical national defense infrastructure. Technology companies must aggressively and transparently police their internal ethical environments to actively prevent the normalization of bribery and corruption, as disastrously witnessed in the RMG recruitment scandal.
4. Comprehensive Regulatory Oversight of Educational Consultancies: Corporate entities actively operating as educational consultancies, especially those publicly claiming massive global university tie-ups to attract clients, must be immediately brought under strict statutory regulation and continuous financial monitoring. The aggressive auditing of these entities is absolutely paramount to detecting the extortionate accumulation of hostage documents (mark sheets), post-dated cheques, and the massive, unregulated cash reserves ultimately used to fund advanced cyber-operations and hire international hackers.
Continued Subversion
The profound subversion of the 2021 JEE (Mains) examination represents a highly sophisticated, dangerous convergence of white-collar corporate fraud, advanced technical cyber-intrusions, and brutal physical extortion. The successful arrest of Siddharth Krishna, Vishwambhar Mani Tripathi, and Govind Varshney—the three directing architects of the Noida-based Affinity Education Private Limited—effectively dismantled a highly predatory syndicate that mercilessly weaponized the intense socio-economic pressures defining Indian higher education.
Operating with near impunity from Noida, a rapidly expanding region demonstrating immense dual-use technological capacity and serving as a known haven for transnational cyber scams, this specific corporate entity successfully blended archaic physical extortion tactics (the withholding of original academic mark sheets and post-dated cheques) with cutting-edge cyber warfare techniques. This dangerous evolution culminated in the unprecedented use of foreign cyber-mercenaries to systematically breach ostensibly secure, enterprise-grade platforms such as iLeon.
When meticulously analyzed alongside the catastrophic insider threats demonstrated in the Rajasthan Jail Prahari examination leaks, the blatant TeamViewer compromises in the regional SSC exams, and the massive internal corporate bribery scandals severely plaguing the very platform providers entrusted with the system's security, the Affinity Education case definitively ceases to be an isolated, anomalous incident. Instead, it serves as a glaring, undeniable diagnostic indicator of the profound systemic vulnerabilities inherently present in outsourcing the nation's academic meritocracy to interconnected digital platforms that fundamentally lack absolute, verifiable zero-trust verification.
Moving forward into an increasingly digital future, securing the absolute integrity of computer-based testing requires significantly more than just deploying superior software engineering.
Only through this comprehensive restructuring can the promise of digital equity in educational assessments be genuinely realized and permanently secured against the relentless innovation of academic cybercrime.









